A quarter of cyber incidents reported to Australian security officials over the past year have targeted critical infrastructure and essential services, including health care, food distribution and energy.
The Australian Cyber Security Centre (ACSC) disclosed the incidents in a report published yesterday, warning of “significant targeting, both domestically and globally, of essential services.”
These incidents have “underscored the vulnerability of critical infrastructure to significant disruption in essential services, lost revenue and the potential of harm or loss of life.”

Photo: Bloomberg
The report will also show ransomware attacks disclosed to the ACSC increased 15 percent in the 2020-21 financial year, when compared with the previous financial year.
The ACSC — which is part of the Australian Signals Directorate — received more than 67,500 reports of cybercrime of all types in 2020-21, or one every eight minutes.
That compared with one every 10 minutes the previous year.
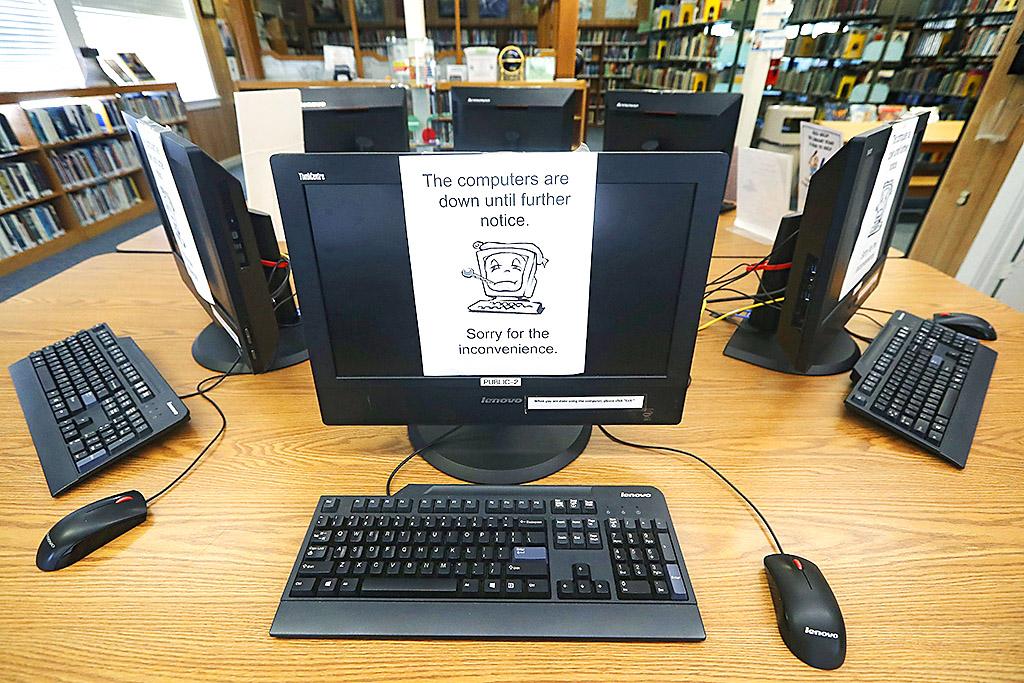
Photo: AP
HUGE LOSSES
The report says businesses, individuals and other entities had incurred more than US$33 billion in total losses from cyber crime throughout the year.
Cybercriminals sought to exploit the pandemic by encouraging recipients to enter personal credentials to access COVID-related information or services, while unnamed foreign governments targeted the health sector seeking “access to intellectual property or sensitive information about Australia’s response to COVID.”

Photo: AFP
The ACSC responded to about 1,630 cybersecurity incidents in 2020-21, or an average of 31 cybersecurity incidents a week.
“Approximately one quarter of reported cybersecurity incidents affected critical infrastructure organizations, including essential services such as education, health, communications, electricity, water and transport,” the report says.
A breakdown of the severity of cyber incidents in 2020-21 shows there were 14 cases in which federal government entities or nationally significant infrastructure suffered the removal or damage of sensitive data or intellectual property.
This category also includes the supply chain to critical national infrastructure. Those entities also suffered a further 44 incidents in which there was an active network intrusion or temporary disruption to systems or services.
The report does not name most of the affected entities, although it includes several case studies, including a March 2021 ransomware attack against a Victorian public health service. That attack “affected four hospitals and aged care facilities, and resulted in the postponement of elective surgeries.”
The assistant defense minister, Andrew Hastie, who released the report, said malicious cyber criminals were “escalating their attacks on Australians”.
Hastie said the health sector reported the second highest number of ransomware incidents, “right at a time when Australians are most reliant on our health workers to help us respond and recover through the pandemic.”
He pointed to a government bill — which remains before the parliament, and has attracted concerns from industry about regulatory impact — that would impose mandatory cyber incident reporting requirements on organizations that run critical infrastructure assets.
Hastie said the legislation would “ensure that in the event of a large-scale cyber attack on our critical infrastructure, our cyber and law enforcement agencies are empowered to provide greater and more immediate support to the victims.”
In ransomware attacks, criminals typically lock up the data of a target organization and then demand payment to decrypt and unlock systems, sometimes threatening to leak stolen data if the request is rebuffed.
The ACSC report mentions the ransomware attack on the global meat and food processing company JBS Foods in May 2021, which led to the suspension of operations and standing down of workers in Australia.
The US division later confirmed that it had paid a ransom equivalent to US$11 million — reportedly in bitcoin.
With nearly 500 ransomware cybercrime reports in the 2020-21 financial year, the ACSC says the problem has “grown in profile and impact, and poses one of the most significant threats to Australian organizations.”
“This increase has been associated with an increasing willingness of criminals to extort money from particularly vulnerable and critical elements of society.”
The report says ransom demands by cybercriminals ranged from thousands to millions of dollars, and attackers have improved their capabilities by accessing tools and services on the dark web.
The report says “new and serious concerns” have joined the list of existing cyber threats, such as “the protection of Australia’s COVID-19 vaccine supply, including distribution processes, from malicious cyber actors.”
STATE-BASED ACTORS
State-based actors are believed to have an interest in learning more about Australia’s pandemic response and the views of those providing advice to government.
“State and criminal cyber actors alike possess the capability to disrupt Australia’s critical infrastructure — including vaccine supply and distribution chains — with the pandemic only amplifying the opportunities for these actors to cause Australia harm,” the report says.
“Even in the absence of direct and intentional targeting, there remains the potential for malicious cyber actors to inadvertently disrupt vaccine supply and distribution chains, making the threat more difficult to address.”
The report mentions China once — when summarizing the Australian government’s decision in July to join with the US and other international partners in accusing China’s Ministry of State Security of exploiting vulnerabilities in the Microsoft Exchange software.
That exploit is estimated to have affected thousands of computers and networks worldwide, including in Australia — but the Chinese government said they were “groundless accusations.”
Wednesday’s report also warns that business email compromise — which includes when companies are targeted with fake invoices that appear to be for genuine services — “continues to present a major threat to Australian businesses and government enterprises, especially as more Australians work remotely.”
The average loss in such incidents was more than US$50,600, which the report says is “over one-and-a-half times higher than the previous financial year.” It says cybercriminal groups have become more sophisticated and organized.

Most heroes are remembered for the battles they fought. Taiwan’s Black Bat Squadron is remembered for flying into Chinese airspace 838 times between 1953 and 1967, and for the 148 men whose sacrifice bought the intelligence that kept Taiwan secure. Two-thirds of the squadron died carrying out missions most people wouldn’t learn about for another 40 years. The squadron lost 15 aircraft and 148 crew members over those 14 years, making it the deadliest unit in Taiwan’s military history by casualty rate. They flew at night, often at low altitudes, straight into some of the most heavily defended airspace in Asia.

This month the government ordered a one-year block of Xiaohongshu (小紅書) or Rednote, a Chinese social media platform with more than 3 million users in Taiwan. The government pointed to widespread fraud activity on the platform, along with cybersecurity failures. Officials said that they had reached out to the company and asked it to change. However, they received no response. The pro-China parties, the Chinese Nationalist Party (KMT) and Taiwan People’s Party (TPP), immediately swung into action, denouncing the ban as an attack on free speech. This “free speech” claim was then echoed by the People’s Republic of China (PRC),

Many people in Taiwan first learned about universal basic income (UBI) — the idea that the government should provide regular, no-strings-attached payments to each citizen — in 2019. While seeking the Democratic nomination for the 2020 US presidential election, Andrew Yang, a politician of Taiwanese descent, said that, if elected, he’d institute a UBI of US$1,000 per month to “get the economic boot off of people’s throats, allowing them to lift their heads up, breathe, and get excited for the future.” His campaign petered out, but the concept of UBI hasn’t gone away. Throughout the industrialized world, there are fears that
Like much in the world today, theater has experienced major disruptions over the six years since COVID-19. The pandemic, the war in Ukraine and social media have created a new normal of geopolitical and information uncertainty, and the performing arts are not immune to these effects. “Ten years ago people wanted to come to the theater to engage with important issues, but now the Internet allows them to engage with those issues powerfully and immediately,” said Faith Tan, programming director of the Esplanade in Singapore, speaking last week in Japan. “One reaction to unpredictability has been a renewed emphasis on