The revelation that the US’ National Security Agency (NSA) was able to eavesdrop on the communications of Google and Yahoo users without breaking into the companies’ data centers sounded like something from a Robert Ludlum spy thriller.
How on earth, the companies asked, did the NSA get their data without their knowing about it?
The most likely answer is a modern spin on a century-old eavesdropping tradition.
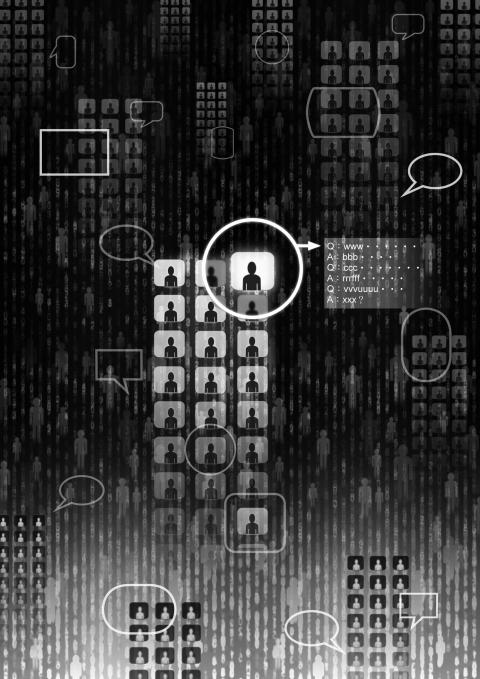
Illustration: Yusha
People knowledgeable about Google and Yahoo’s infrastructure say they believe that government spies bypassed the big Internet companies and hit them at a weak spot — the fiber-optic cables that connect data centers around the world that are owned by companies like Verizon Communications, the BT Group, the Vodafone Group and Level 3 Communications. In particular, fingers have been pointed at Level 3, the world’s largest so-called Internet backbone provider, whose cables are used by Google and Yahoo.
The Internet companies’ data centers are locked down with full-time security and state-of-the-art surveillance, including heat sensors and iris scanners. However, between the data centers — on Level 3’s fiber-optic cables that connected those massive computer farms — information was unencrypted and an easier target for government interception efforts, according to three people with knowledge of Google’s and Yahoo’s systems who spoke on condition of anonymity.
It is impossible to say for certain how the NSA managed to get Google’s and Yahoo’s data without the companies’ knowledge. However, in response to concerns over those vulnerabilities, both companies recently said they had begun encrypting data that runs on the cables between their data centers. Microsoft is considering a similar move.
“Everyone was so focused on the NSA secretly getting access to the front door that there was an assumption they weren’t going behind the companies’ backs and tapping data through the back door, too,” said Kevin Werbach, an associate professor at the Wharton School.
Data transmission lines have a long history of being tapped.
As far back as the days of the telegraph, spy agencies have located their operations in proximity to communications companies. Indeed, before the advent of the Internet, the NSA and its predecessors for decades operated listening posts next to the long-distance lines of phone companies to monitor international voice traffic.
Beginning in the 1960s, a spy operation code-named Echelon targeted the Soviet Union and its allies’ voice, fax and data traffic.
In the 1990s, the emergence of the Internet both complicated the task of the intelligence agencies and presented powerful new spying opportunities based on the ability to process vast amounts of computer data.
In 2002, John Poindexter, who had been national security adviser under former president Ronald Reagan, proposed the Total Information Awareness plan, an effort to scan the world’s electronic information — including phone calls, e-mails and financial and travel records. That effort was scrapped in 2003 after a public outcry over potential privacy violations.
The technologies Poindexter proposed were similar to what became reality years later in NSA surveillance programs like Prism and Bullrun.
The Internet effectively mingled domestic and international communications, erasing the bright line that had been erected to protect against domestic surveillance. Although the Internet is designed to be a highly decentralized system, in practice a small group of backbone providers carry almost all of the network’s data.
The consequences of the centralization and its value for surveillance was revealed in 2006 by Mark Klein, an AT&T technician who described an NSA listening post inside a room at an AT&T switching facility.
The agency was capturing a copy of all the data passing over the telecommunications links and then filtering it in AT&T facilities.
Documents taken by Edward Snowden and reported by the Washington Post indicate that, seven years after Klein first described the NSA’s surveillance technologies, they have been refined and modernized.
“From Echelon to Total Information Awareness to Prism, all these programs have gone under different names but in essence do the same thing,” said Chip Pitts, a law lecturer at Stanford University School of Law.
Based in the Denver suburbs, Level 3 is not a household name like Verizon or AT&T, but in terms of its ability to carry traffic, it is bigger than the other two carriers combined. Its networking equipment is found in 200 data centers in the US, more than 100 centers in Europe and 14 in Latin America.
Level 3 did not directly respond to an inquiry about whether it had given the NSA, or the agency’s foreign intelligence partners, access to Google and Yahoo’s data. In a statement, Level 3 said: “It is our policy and our practice to comply with laws in every country where we operate and to provide government agencies access to customer data only when we are compelled to do so by the laws in the country where the data is located.”
Also, in a financial filing, Level 3 said that, “We are party to an agreement with the US Departments of Homeland Security, Justice and Defense addressing the US government’s national security and law enforcement concerns. This agreement imposes significant requirements on us related to information storage and management; traffic management; physical, logical and network security arrangements; personnel screening and training; and other matters.”
Security experts say that regardless of whether Level 3’s participation is voluntary, recent NSA disclosures make clear that even when Internet giants like Google and Yahoo do not hand over data, the NSA and its intelligence partners can simply gather their data downstream.
That much was true last summer when US authorities began tracking Snowden’s movements after he left Hawaii for Hong Kong with thousands of classified documents. In May, authorities contacted Ladar Levison, who ran Lavabit, Snowden’s e-mail provider, to install a tap on Snowden’s e-mail account. When Levison did not move quickly enough to facilitate the tap on Lavabit’s network, the FBI did so without him.
Levison said it was unclear how that tap was installed, whether through Level 3, which sold bandwidth to Lavabit, or at the Dallas facility where his servers and networking equipment are stored. When Levison asked the facility’s manager about the tap, he was told the manager could not speak with him. A spokesman for TierPoint, which owns the Dallas facility, did not return a call seeking a comment.
Pitts said that while working as the chief legal officer at Nokia in the 1990s, he successfully fended off an effort by intelligence agencies to get backdoor access into Nokia’s computer networking equipment.
Nearly 20 years later, Verizon has said that it and other carriers are forced to comply with government requests in every country in which they operate and are limited in what they can say about their arrangements.
“At the end of the day, if the Justice Department shows up at your door, you have to comply,” Verizon chief executive Lowell McAdam said in an interview in September. “We have gag orders on what we can say and can’t defend ourselves, but we were told they do this with every carrier.”
US President Donald Trump and Chinese President Xi Jinping (習近平) were born under the sign of Gemini. Geminis are known for their intelligence, creativity, adaptability and flexibility. It is unlikely, then, that the trade conflict between the US and China would escalate into a catastrophic collision. It is more probable that both sides would seek a way to de-escalate, paving the way for a Trump-Xi summit that allows the global economy some breathing room. Practically speaking, China and the US have vulnerabilities, and a prolonged trade war would be damaging for both. In the US, the electoral system means that public opinion
They did it again. For the whole world to see: an image of a Taiwan flag crushed by an industrial press, and the horrifying warning that “it’s closer than you think.” All with the seal of authenticity that only a reputable international media outlet can give. The Economist turned what looks like a pastiche of a poster for a grim horror movie into a truth everyone can digest, accept, and use to support exactly the opinion China wants you to have: It is over and done, Taiwan is doomed. Four years after inaccurately naming Taiwan the most dangerous place on
In their recent op-ed “Trump Should Rein In Taiwan” in Foreign Policy magazine, Christopher Chivvis and Stephen Wertheim argued that the US should pressure President William Lai (賴清德) to “tone it down” to de-escalate tensions in the Taiwan Strait — as if Taiwan’s words are more of a threat to peace than Beijing’s actions. It is an old argument dressed up in new concern: that Washington must rein in Taipei to avoid war. However, this narrative gets it backward. Taiwan is not the problem; China is. Calls for a so-called “grand bargain” with Beijing — where the US pressures Taiwan into concessions
The term “assassin’s mace” originates from Chinese folklore, describing a concealed weapon used by a weaker hero to defeat a stronger adversary with an unexpected strike. In more general military parlance, the concept refers to an asymmetric capability that targets a critical vulnerability of an adversary. China has found its modern equivalent of the assassin’s mace with its high-altitude electromagnetic pulse (HEMP) weapons, which are nuclear warheads detonated at a high altitude, emitting intense electromagnetic radiation capable of disabling and destroying electronics. An assassin’s mace weapon possesses two essential characteristics: strategic surprise and the ability to neutralize a core dependency.