The Executive Yuan yesterday unveiled guidelines asking central and local government agencies to tally in-use information and communications technology devices that could pose a risk to the nation’s information security and disconnect any potentially hazardous devices from government networks.
The check should be completed within three months based on assessments of the risks the devices could pose to the government’s operations and social security, Executive Yuan spokeswoman Kolas Yotaka told a news conference in Taipei.
Any device deemed to pose an information security risk whose life span has expired should be replaced and disposed of before the end of this fiscal year, while a timetable for elimination should be set for devices that have not reached the end of their lives, she said.

Photo: CNA
The Guidelines Restricting the Use of Products Threatening Information and Communication Safety went into effect on Thursday afternoon after they were signed by Premier Su Tseng-chang (蘇貞昌), Kolas said.
They apply to government agencies, state-run enterprises and science parks whose work is related to eight categories of key infrastructure: water, energy, communications, transportation, finance, science parks, government agencies and emergency medical services, she said.
Devices that are to be regulated include servers, webcams, drones, cloud-based applications, backbone networks, software and antivirus software, as well as systems whose development has been contracted out, she added.
As guidelines are a type of lower-ranking law, they do not include any punishments for local governments that fail to comply, Kolas said, adding that the Executive Yuan could only encourage local administrations to adhere to the guidelines.
However, relevant agencies are compiling a list of information and communications technology device manufacturers that would be banned from government use, Kolas said.
They are also considering introducing enforcement rules to complement the list, meaning that there would be consequences — for example, administrative fines or lawsuits — for local governments that procure products made by companies on the list, she said.
The list would be published in three months at the earliest, she added.
The Executive Yuan originally targeted only products made by Chinese companies, but later widened the scope to include all products manufactured overseas that could threaten the nation’s information security, Kolas said.
Also being deliberated is whether the central government should introduce a total ban on devices manufactured in China, or only those made by Chinese information and communications technology companies, she said.
Brands that are under review and could make the list include ZTE Corp (中興通訊), Lenovo Group (聯想) and Hikvision Digital Technology Co (海康威視), an official familiar with the matter said.
Asked whether the ban should also be followed by private companies whose work or services involve the eight categories of key infrastructure, Kolas said that they and their governing agencies should work out an agreement.
For example, the National Communications Commission should discuss the issue with privately run telecoms, such as Taiwan Mobile Co (台灣大哥大), as should science park administration offices with firms in the parks, she said.

A Ministry of Foreign Affairs official yesterday said that a delegation that visited China for an APEC meeting did not receive any kind of treatment that downgraded Taiwan’s sovereignty. Department of International Organizations Director-General Jonathan Sun (孫儉元) said that he and a group of ministry officials visited Shenzhen, China, to attend the APEC Informal Senior Officials’ Meeting last month. The trip went “smoothly and safely” for all Taiwanese delegates, as the Chinese side arranged the trip in accordance with long-standing practices, Sun said at the ministry’s weekly briefing. The Taiwanese group did not encounter any political suppression, he said. Sun made the remarks when

PREPAREDNESS: Given the difficulty of importing ammunition during wartime, the Ministry of National Defense said it would prioritize ‘coproduction’ partnerships A newly formed unit of the Marine Corps tasked with land-based security operations has recently replaced its aging, domestically produced rifles with more advanced, US-made M4A1 rifles, a source said yesterday. The unnamed source familiar with the matter said the First Security Battalion of the Marine Corps’ Air Defense and Base Guard Group has replaced its older T65K2 rifles, which have been in service since the late 1980s, with the newly received M4A1s. The source did not say exactly when the upgrade took place or how many M4A1s were issued to the battalion. The confirmation came after Chinese-language media reported
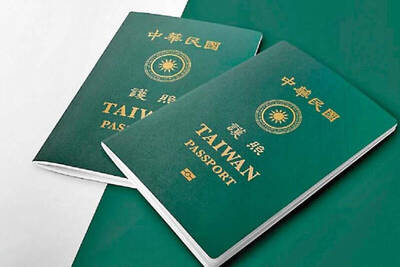
The Taiwanese passport ranked 33rd in a global listing of passports by convenience this month, rising three places from last month’s ranking, but matching its position in January last year. The Henley Passport Index, an international ranking of passports by the number of designations its holder can travel to without a visa, showed that the Taiwan passport enables holders to travel to 139 countries and territories without a visa. Singapore’s passport was ranked the most powerful with visa-free access to 192 destinations out of 227, according to the index published on Tuesday by UK-based migration investment consultancy firm Henley and Partners. Japan’s and

BROAD AGREEMENT: The two are nearing a trade deal to reduce Taiwan’s tariff to 15% and a commitment for TSMC to build five more fabs, a ‘New York Times’ report said Taiwan and the US have reached a broad consensus on a trade deal, the Executive Yuan’s Office of Trade Negotiations said yesterday, after a report said that Washington is set to reduce Taiwan’s tariff rate to 15 percent. The New York Times on Monday reported that the two nations are nearing a trade deal to reduce Taiwan’s tariff rate to 15 percent and commit Taiwan Semiconductor Manufacturing Co (TSMC, 台積電) to building at least five more facilities in the US. “The agreement, which has been under negotiation for months, is being legally scrubbed and could be announced this month,” the paper said,