The shady world of the virus writer is changing. Programmers of computer viruses used to do it for fun, out of intellectual curiosity, or just bloody-mindedness, infecting computers with malevolent code because they could.
But now there are worrying signs that virus writing has evolved into a lucrative industry, with spammers, mobsters and blackmailers in on the act.
"What we've seen in the past 18 months or so is a shift in the way viruses work," says Graham Cluley, senior technology consultant at Sophos, the UK-based anti-virus company. "It's all about money."
Yesterday's viruses carried isolated payloads, which could be anything from displaying a benign message on the screen to wiping your hard drive. Once the payload had been delivered and the virus had copied itself to another machine, its work was done.
Today's malware is often different: it creates a back door on a PC, enabling hackers to control it over the Internet and use it for nefarious purposes.
"Zombies," or "bots," PCs that have been infected in this way, are being used to make money for a new generation of criminal, explains Alex Shipp, senior anti-virus technologist at MessageLabs.
For example, "the hackers will change the phone number your PC's modem dials to dial an expensive number and make money for them. If you are using broadband, that's even better, because you have a fast connection to the Internet. They can use your computer to send out spam and charge people for the service."
Spammers prefer to send unsolicited commercial email from compromised machines on "botnets" because it makes it more difficult for recipients to block the mail, and it protects the spammers' servers from being tracked and shut down. Networks of tens of thousands of Windows PCs are used for such purposes.
Telenor, an ISP, recently shut down a 10,000-strong botnet of computers controlled over the Internet Relay Chat (IRC) network.
Once a team of virus writers has grown its botnet to a sufficient size, it can sell it as a resource.
Sales of "botnet time" between criminals are often conducted through covert negotiations on IRC, the very mechanism used to control the botnets.
Internet worms are now becoming increasingly sophisticated in their attempts to recruit desktop PCs into botnets.
One of the latest, Bofra, sets up its own Web server on an infected PC and then e-mails its address to contacts in the PC's e-mail address book. When recipients click on the e-mail -- which has no virus inside it -- they are taken to the infected PC, which in turn tries to infect their computers.
Each infected computer listens on the IRC network for hackers that want to take control of it.
The spread of Bofra has been limited, and corporate machines are unlikely to be infected by it because of weaknesses in the way it works.
However, that doesn't matter, says Pete Simpson, Threatlab manager at Clearswift, an e-mail security software company.
"It's the unprotected PCs -- the soft underbelly of the Internet -- that have been infected," he said.
"These crooks are not interested in collecting owned corporate PCs. They are gathering a free resource that can be sold on for spamming attacks," he said.
The sort of people who use Windows PCs that have not been patched with recent updates, including SP2, and who don't have firewalls, are also the ones who may not notice their PC is being used for spamming, and won't know how to respond.
Spamming isn't the only reason for collecting zombie PCs. Some criminals marshal "their" machines to mount distributed denial of service attacks on corporate computers, blackmailing the victims before they will stop the attacks. Web sites of several online betting companies have been attacked recently.
Botnet machines can also be used as free Web hosts, says Miko Hypponnen, head of anti-virus research at F-Secure, a security firm.
"These guys use infected computers to run Web sites selling hardcore porn and illegal goods," Hypponnen said.
Who is behind this fast-growing criminal industry? Many of the groups come from Eastern Europe or Russia, and the UK's National High-Tech Crime Unit (NHTCU) has in the past year arrested dozens of people connected with identity theft and extortion through denial of service attacks.

ROLLER-COASTER RIDE: More than five earthquakes ranging from magnitude 4.4 to 5.5 on the Richter scale shook eastern Taiwan in rapid succession yesterday afternoon Back-to-back weather fronts are forecast to hit Taiwan this week, resulting in rain across the nation in the coming days, the Central Weather Administration said yesterday, as it also warned residents in mountainous regions to be wary of landslides and rockfalls. As the first front approached, sporadic rainfall began in central and northern parts of Taiwan yesterday, the agency said, adding that rain is forecast to intensify in those regions today, while brief showers would also affect other parts of the nation. A second weather system is forecast to arrive on Thursday, bringing additional rain to the whole nation until Sunday, it

LANDSLIDES POSSIBLE: The agency advised the public to avoid visiting mountainous regions due to more expected aftershocks and rainfall from a series of weather fronts A series of earthquakes over the past few days were likely aftershocks of the April 3 earthquake in Hualien County, with further aftershocks to be expected for up to a year, the Central Weather Administration (CWA) said yesterday. Based on the nation’s experience after the quake on Sept. 21, 1999, more aftershocks are possible over the next six months to a year, the agency said. A total of 103 earthquakes of magnitude 4 on the local magnitude scale or higher hit Hualien County from 5:08pm on Monday to 10:27am yesterday, with 27 of them exceeding magnitude 5. They included two, of magnitude

CONDITIONAL: The PRC imposes secret requirements that the funding it provides cannot be spent in states with diplomatic relations with Taiwan, Emma Reilly said China has been bribing UN officials to obtain “special benefits” and to block funding from countries that have diplomatic ties with Taiwan, a former UN employee told the British House of Commons on Tuesday. At a House of Commons Foreign Affairs Committee hearing into “international relations within the multilateral system,” former Office of the UN High Commissioner for Human Rights (OHCHR) employee Emma Reilly said in a written statement that “Beijing paid bribes to the two successive Presidents of the [UN] General Assembly” during the two-year negotiation of the Sustainable Development Goals. Another way China exercises influence within the UN Secretariat is
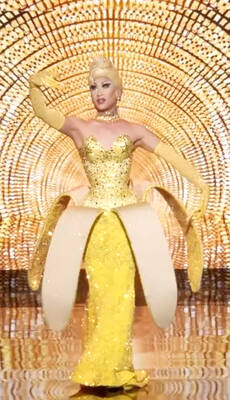
Taiwan’s first drag queen to compete on the internationally acclaimed RuPaul’s Drag Race, Nymphia Wind (妮妃雅), was on Friday crowned the “Next Drag Superstar.” Dressed in a sparkling banana dress, Nymphia Wind swept onto the stage for the final, and stole the show. “Taiwan this is for you,” she said right after show host RuPaul announced her as the winner. “To those who feel like they don’t belong, just remember to live fearlessly and to live their truth,” she said on stage. One of the frontrunners for the past 15 episodes, the 28-year-old breezed through to the final after weeks of showcasing her unique