Taiwan is the front line in an emerging global battle for cyberspace, according to elite hackers in the country’s IT industry, who say it has become a rehearsal area for the Chinese cyberattacks that have strained ties with the US.
Taiwan has endured at least a decade of highly targeted data-theft attacks that are then directed towards larger countries, they say.
“We’ve seen everything,” said Jim Liu, the 28-year-old founder of Lucent Sky, a Taiwanese Internet security company specializing in resolving dangerous software vulnerabilities that hackers can exploit to gain access to a system. “We’ll see a specific attack signature here, and then six months later, see the same signature in an attack on the States.”
A Pentagon report in May accused China of trying to break into US defense computer networks. It followed another report in February by US computer security company Mandiant that said a secretive Chinese military unit was probably behind a series of hacking attacks that had stolen data from about 100 US companies.
Beijing dismissed both reports as without foundation. Taiwan experts say that hacking methods such as those outlined in the Mandiant report are the same kinds of security breaches that they had seen several years earlier.
It is easy to see why Taiwan might be an ideal target for Chinese hackers: It is close to China, Mandarin-speaking and boasts advanced Internet infrastructure.
This cyberwar playing out across the Taiwan Strait first came to public attention in 2003, when a Taiwanese police agency realized hackers had stolen personal data, including household registration information, from its computer system.
These attacks differed from traditional hacking attempts — where many casual hackers attempt to disrupt their targets’ systems, these hackers went in stealthily, with the intention to plunder, rather than destroy.
“Back then, it was very rare to see these kinds of social network attacks,” said hacking specialist Jeremy Chiu, a contract instructor in IT for Taiwan’s intelligence agencies. “They were very, very well-organized.”
Other indicators, including the ease with which the hackers penetrated an e-mail system written entirely in Chinese, painted a picture of the culprits as a large, coordinated group of hackers in China.
“One thing that indicates government support for these attacks is just the sheer volume — how many agencies are being attacked on a daily basis,” said Benson Wu, postdoctoral researcher in information technology at Academia Sinica and co-founder of Xecure Lab, which focuses on responding to advanced persistent threats.
The set-up of Wu’s Taipei office fits the classic hacker image: dimly lit, strewn with wires and humming with computers.
On a projector screen, he displayed a list of e-mails, written in Chinese, with subject headings like “meeting notes,” “dinner attendance” and “questionnaire.”
“These are all hacking attempts,” Wu said.
Once the documents have been opened, they plant a backdoor allowing the hacker virtually unfettered access to the network.
One such “spearphishing” attack was reportedly used on the White House in October last year. A Taiwanese expert in cyberespionage estimated that thousands of Taiwanese high-level government employees receive as many as between 20 and 30 of these e-mails a month.
“We’ve been following these Chinese hackers for so long, we can track their daily work schedule,” said the expert, who asked not to be identified. “People expect hackers to be night owls, but these guys work very normal hours — on Chinese national holidays, for example, we don’t see any hacking activity at all.”
However, tracking the exact source of the attacks remains a slippery game of Internet sleuth.
“We take the IP address culled from the attack as a springboard, then track it through the Internet — perhaps the same IP address was used in a forum registration, or to register a QQ handle,” he said, referring to a popular Chinese chat program. “It depends how good they are at covering their tracks.”
China denies being behind hacking attacks on other nations and insists it is a major victim of cyberattacks, including from the US — an argument that Beijing sees as strengthened by revelations last month from former National Security Agency contractor Edward Snowden about top-secret US electronic surveillance programs.
The US and China held talks focused on cyberissues last week.
According to Internet platform Akamai, 27 percent of worldwide hacking activity last year originated in China. However, the same report also placed Taiwan among the top five digital attack originating countries last year.
“Taiwan is one of the key countries where we see a lot of activity,” Singapore-based malware researcher Chong Rong Hwa of network security firm FireEye Inc said.
A report issued by SecureWorks, a network safety arm of PC maker Dell Inc, said the Taiwanese government’s ministries are swarming with a particularly malicious form of data-nabbing computer virus.
In one year, Taiwan’s National Security Bureau encountered more than 3 million hacking attempts from China, according to statements given by bureau director Tsai Der-sheng (蔡得勝) in March in response to questions from lawmakers.
Military and technology intelligence was included among the pilfered data.
“Taiwan will continue to be the battleground for lots of cyberattacks; it’s like we are on our own,” Wu said. “China has a huge pool of talent and technical resources.”

A group of Taiwanese-American and Tibetan-American students at Harvard University on Saturday disrupted Chinese Ambassador to the US Xie Feng’s (謝鋒) speech at the school, accusing him of being responsible for numerous human rights violations. Four students — two Taiwanese Americans and two from Tibet — held up banners inside a conference hall where Xie was delivering a speech at the opening ceremony of the Harvard Kennedy School China Conference 2024. In a video clip provided by the Coalition of Students Resisting the CCP (Chinese Communist Party), Taiwanese-American Cosette Wu (吳亭樺) and Tibetan-American Tsering Yangchen are seen holding banners that together read:

UNAWARE: Many people sit for long hours every day and eat unhealthy foods, putting them at greater risk of developing one of the ‘three highs,’ an expert said More than 30 percent of adults aged 40 or older who underwent a government-funded health exam were unaware they had at least one of the “three highs” — high blood pressure, high blood lipids or high blood sugar, the Health Promotion Administration (HPA) said yesterday. Among adults aged 40 or older who said they did not have any of the “three highs” before taking the health exam, more than 30 percent were found to have at least one of them, Adult Preventive Health Examination Service data from 2022 showed. People with long-term medical conditions such as hypertension or diabetes usually do not

POLICE INVESTIGATING: A man said he quit his job as a nurse at Taipei Tzu Chi Hospital as he had been ‘disgusted’ by the behavior of his colleagues A man yesterday morning wrote online that he had witnessed nurses taking photographs and touching anesthetized patients inappropriately in Taipei Tzu Chi Hospital’s operating theaters. The man surnamed Huang (黃) wrote on the Professional Technology Temple bulletin board that during his six-month stint as a nurse at the hospital, he had seen nurses taking pictures of patients, including of their private parts, after they were anesthetized. Some nurses had also touched patients inappropriately and children were among those photographed, he said. Huang said this “disgusted” him “so much” that “he felt the need to reveal these unethical acts in the operating theater
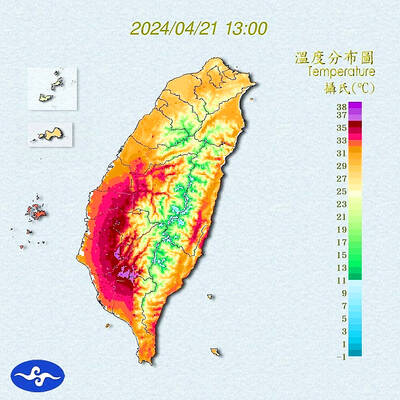
Heat advisories were in effect for nine administrative regions yesterday afternoon as warm southwesterly winds pushed temperatures above 38°C in parts of southern Taiwan, the Central Weather Administration (CWA) said. As of 3:30pm yesterday, Tainan’s Yujing District (玉井) had recorded the day’s highest temperature of 39.7°C, though the measurement will not be included in Taiwan’s official heat records since Yujing is an automatic rather than manually operated weather station, the CWA said. Highs recorded in other areas were 38.7°C in Kaohsiung’s Neimen District (內門), 38.2°C in Chiayi City and 38.1°C in Pingtung’s Sandimen Township (三地門), CWA data showed. The spell of scorching