As few as 12 different Chinese groups, largely backed or directed by the government, do the bulk of the China-based cyberattacks stealing critical data from US companies and government agencies, according to US cybersecurity analysts and experts.
The aggressive, but stealthy attacks, which steal billions of US dollars in intellectual property and data, often carry distinct signatures allowing US officials to link them to certain hacker teams. And, analysts say the US often gives the attackers unique names or numbers and at times can tell where the hackers are and even who they might be.
Sketched out by analysts who have worked with US companies and the government on computer intrusions, the details illuminate recent claims by US intelligence officials about the escalating cyberthreat emanating from China. And the widening expanse of targets, coupled with the expensive and sensitive technologies they are losing, is putting increased pressure on the US to take a much harder stand against Beijing.
It is impossible for the US to prosecute hackers in China, since it requires reciprocal agreements between the two countries and it is always difficult to provide ironclad proof that the hacking came from specific people.
Several analysts described the Chinese attacks, speaking on condition of anonymity because of the sensitivity of the investigations and to protect the privacy of clients. China has routinely rejected allegations of cyberspying and says it is also a target.
“Industry is already feeling that they are at war,” said James Cartwright, a retired US Marine General and former Joint Chiefs of Staff vice chairman.
A recognized expert on cyberissues, Cartwright has come out strongly in favor of increased US efforts to hold China and other countries accountable for the cyberattacks that come from within their borders.
“Right now we have the worst of worlds,” Cartwright said. “If you want to attack me you can do it all you want, because I can’t do anything about it. It’s risk free and you’re willing to take almost any risk to come after me.”
He said the US “needs to say: ‘If you come after me, I’m going to find you, I’m going to do something about it. It will be proportional, but I’m going to do something ... and if you’re hiding in a third country, I’m going to tell that country you’re there, if they don’t stop you from doing it, I’m going to come and get you.’”
Cyberexperts agree and say that companies are frustrated that the government is not doing enough to pressure China to stop the attacks or go after hackers in that country.
Much like during the Cold War with Russia, officials say the US needs to make it clear that there will be repercussions for cyberattacks.
The government “needs to do more to increase the risk,” said Jon Ramsey, head of the counter threat unit at the Atlanta-based Dell SecureWorks, a computer security consulting company. “In the private sector we’re always on defense. We can’t do something about it, but someone has to. There is no deterrent not to attack the US.”
Cyberattacks originating in China have been a problem for years, but until a decade or so ago analysts said the probes focused mainly on the US government — a generally acknowledged intelligence gathering activity similar to the US and Russia spying on each other during the Cold War.
However, in the past 10 to 15 years, the attacks have gradually broadened to target defense companies and then other critical industries, including those in energy, finance and other sectors.
According to Ramsey and other cyberanalysts, hackers in China have different digital fingerprints, often visible through the computer code they use or the command and control computers that they use to route their malicious software through.
US government officials have been reluctant to tie the attacks directly back to the Chinese government, but analysts and officials quietly say that they have tracked enough intrusions to specific locations to be confident they are linked to Beijing — either the government or the military. And, they add that they can sometimes glean who benefited from a particular stolen technology.
One of the analysts said investigations show that the dozen or so Chinese teams appear to get “taskings,” or orders, to go after specific technologies or companies within a particular industry. At times, two or more of the teams appear to get the same shopping list and compete to be the first to get it or the one with the greatest haul.
Analysts and US officials agree that a majority of the cyberattacks seeking intellectual property or other sensitive or classified data are done by China-based hackers. While much of the cyberattacks stealing credit card or financial information come from Eastern Europe or Russia.
According to experts, the malicious software or high-tech tools used by the Chinese have not gotten much more sophisticated in recent years. However, the threat is -persistent, often burying malware deep in computer networks so it can be used again and again over the course of several months or even years.
The tools include malware that can record keystrokes, steal and decrypt passwords, as well as copy and compress data so it can be transferred back to the attacker’s computer. The malware can then delete itself or disappear until needed again.
Several specific attacks linked to China include:
Two sophisticated attacks against Google’s systems that stole some of the Internet giant’s intellectual property and broke into the Gmail accounts of several hundred people, including senior US government officials, military personnel and political activists.
Last year computer security firm Mandiant reported that data was stolen from a Fortune 500 manufacturing company during business negotiations when the company was trying to buy a Chinese company.
Earlier this year, McAfee traced an intrusion to an Internet protocol address in China and said intruders took data from global oil, energy and petrochemical companies.
Chinese Foreign Ministry spokesperson, Liu Weimin (劉為民) did not respond yesterday to the specific allegations about government--supported cyberattacks, but said Internet security is an issue the world needs to address collectively.
The international community should “prevent the Internet from becoming a new battlefield,” Liu said at a daily media briefing in Beijing.
For the first time, US intelligence officials called out China and Russia last month, saying they are systematically stealing US high-tech data for their own economic gain.
The next step, Cartwright said, must be a full-throated US policy that makes it clear how the US will deal with cyberattacks, including the attackers as well as the nations the attacks are routed through.

ROLLER-COASTER RIDE: More than five earthquakes ranging from magnitude 4.4 to 5.5 on the Richter scale shook eastern Taiwan in rapid succession yesterday afternoon Back-to-back weather fronts are forecast to hit Taiwan this week, resulting in rain across the nation in the coming days, the Central Weather Administration said yesterday, as it also warned residents in mountainous regions to be wary of landslides and rockfalls. As the first front approached, sporadic rainfall began in central and northern parts of Taiwan yesterday, the agency said, adding that rain is forecast to intensify in those regions today, while brief showers would also affect other parts of the nation. A second weather system is forecast to arrive on Thursday, bringing additional rain to the whole nation until Sunday, it

LANDSLIDES POSSIBLE: The agency advised the public to avoid visiting mountainous regions due to more expected aftershocks and rainfall from a series of weather fronts A series of earthquakes over the past few days were likely aftershocks of the April 3 earthquake in Hualien County, with further aftershocks to be expected for up to a year, the Central Weather Administration (CWA) said yesterday. Based on the nation’s experience after the quake on Sept. 21, 1999, more aftershocks are possible over the next six months to a year, the agency said. A total of 103 earthquakes of magnitude 4 on the local magnitude scale or higher hit Hualien County from 5:08pm on Monday to 10:27am yesterday, with 27 of them exceeding magnitude 5. They included two, of magnitude

CONDITIONAL: The PRC imposes secret requirements that the funding it provides cannot be spent in states with diplomatic relations with Taiwan, Emma Reilly said China has been bribing UN officials to obtain “special benefits” and to block funding from countries that have diplomatic ties with Taiwan, a former UN employee told the British House of Commons on Tuesday. At a House of Commons Foreign Affairs Committee hearing into “international relations within the multilateral system,” former Office of the UN High Commissioner for Human Rights (OHCHR) employee Emma Reilly said in a written statement that “Beijing paid bribes to the two successive Presidents of the [UN] General Assembly” during the two-year negotiation of the Sustainable Development Goals. Another way China exercises influence within the UN Secretariat is
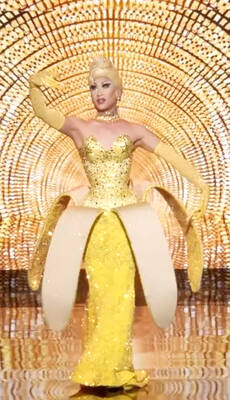
Taiwan’s first drag queen to compete on the internationally acclaimed RuPaul’s Drag Race, Nymphia Wind (妮妃雅), was on Friday crowned the “Next Drag Superstar.” Dressed in a sparkling banana dress, Nymphia Wind swept onto the stage for the final, and stole the show. “Taiwan this is for you,” she said right after show host RuPaul announced her as the winner. “To those who feel like they don’t belong, just remember to live fearlessly and to live their truth,” she said on stage. One of the frontrunners for the past 15 episodes, the 28-year-old breezed through to the final after weeks of showcasing her unique