Troubled by something deeply unethical going on at work? Or maybe you are plotting to leak sensitive information on the company that just sacked you? Either way, you best think twice before making your next move because an all-seeing artificial intelligence (AI) might just be analyzing every e-mail you send, every file you upload, every room you scan into — even your coffee routine.
The latest wave of cyberdefense technology employs machine learning to monitor use of the ever-expanding number of smart household objects connected to the Internet of Things — shutting down hackers before they have broken into corporate databases or whistle-blowers before they have forwarded information to the media.
One of the leading proponents is cyberdefense company Darktrace, founded in 2013 by former British intelligence officers in Cambridge and today featuring 370 employees in 23 offices globally. The company is targeting growth in the Asia-Pacific region, where regional head Sanjay Aurora is promoting Darktrace’s Enterprise Immune System at the CeBIT Australia conference in Sydney on May 23.
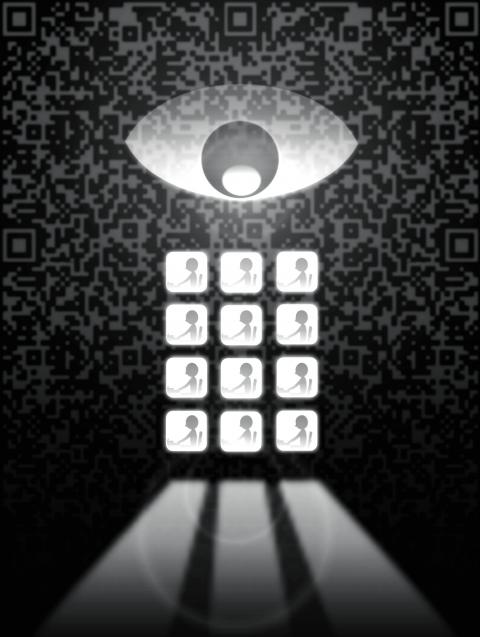
Illustration: Yusha
In an interview ahead of the conference, Aurora told the Guardian that the Internet of Things, the interconnected everyday devices such as the smart refrigerator, offers more vulnerabilities to be hacked than ever before — but also more ways to scan for threats.
“In newspapers there is not a single day where we don’t read about an organization being breached,” he said. “At a time when even coffee machines have IP [Internet protocol] addresses, many people in security teams don’t so much as have visibility of the network.”
Where cybersecurity normally functions as a barrier to keep out previously identified threats, Aurora said Darktrace technology behaves more like a human immune system.
“Once you understand the devices and people, once you notice subtle changes within the network, you establish a pattern of life, and whether it is lateral movement or unusual activity — maybe an employee using a device they don’t normally use, or a fingerprint scanner acting unusually — the immune system notices and takes action, detecting these things in network before they become a headline,” he said.
Darktrace’s package includes a 3D topographical real-time “threat visualizer” that monitors everyday network activity and the responsive Antigena system, which can decide for itself to slow systems down to give security personnel time to stop a potential breach, cut off network access to particular individuals, or mark specific e-mails for further investigation.
“Let’s say an employee is made redundant and becomes a potential information threat, the machine will intelligently determine what is the problem, assess the mathematical threat and then decide what action is to be taken,” Aurora said.
Darktrace says its Enterprise Immune System has reported more than 30,000 serious cyberincidents in more than 2,000 deployments across the world, offering examples such as an employee who was disgruntled about their company’s Brexit plans and was caught before the person could leak the information.
FINGERPRINTS
Another case was put forward by Darktrace cofounder Poppy Gustafsson at the TechCrunch Disrupt conference in London last year.
Gustafsson cited the case of attackers sending a truck into the warehouse of a luxury goods manufacturer after uploading their fingerprints to the company’s system to bypass the biometric scanners.
“It’s one of the few attacks where a criminal has given their fingerprint ahead of time,” she said.
Darktrace is well on the way to establishing itself in Australia ahead of the CeBIT business tech conference, already boasting clients such as national telecommunications provider Telstra.
A Telstra spokesperson said the company “joined forces with Darktrace last year, adding it to a suite of complementary security technologies that are designed and utilized to protect customer and corporate information and the Telstra network.
Darktrace, along with our other technologies, people and processes, strengthens Telstra’s internal security through its ability to detect anomalous activity and its ability to visualize all network activity, resulting in a reduced time to detect potential threats.”
The move has attracted concern from Communication Workers Union national secretary Greg Rayner, who said the union was not consulted on the introduction of the technology.
“That’s disappointing and arguably a breach of Telstra’s obligations under the current enterprise agreement,” he said. “They’re supposed to consult on changes that will have a significant effect on the workforce. Telstra employees have been subjected to increasingly intense electronic monitoring in recent years, including scrutiny and recording of their online activities at work. We are obviously concerned that this technology will allow further intrusions into employees’ day-to-day working lives.”
Telstra has history in regard to unions and whistle-blowers — in 2008, former employee Jim Ziogas was fired after being connected to a leak to the media of internal plans to de-unionize the workforce.
Whistle-blowers Australia vice president Brian Martin does not have a lot in common with Darktrace, but he does share a fondness for immune-system analogies.
“Whistle-blowers are antibodies for corruption in organizations,” he said. “If it were possible to prevent leaks —and that remains to be shown — this might only allow problems to fester until they become much worse. Think of what happened to Volkswagen, which lacked any whistle-blowers or leakers and paid a much larger penalty than if its emissions fraud had been exposed years earlier.”
He said invading the privacy of workers has the potential to create resentment and undermine loyalty, and that a lack of independent monitoring means there are serious questions regarding the effectiveness of Darktrace’s Enterprise Immune System, particularly in regard to false positives and false negatives.
“The damage to morale done by falsely accusing an employee of planning to leak documents can be imagined,” he said. “How about this option? Adapt the software to monitor the e-communications of top managers to see whether they are planning reprisals against whistle-blowers. How do you think they would like that?”
Devised as it was by former agents from Britain’s MI5 and Government Communications Headquarters, inspired by the challenges they were facing in counterintelligence, Darktrace technology is also an interesting proposition for governments, but the company is more coy about the countries that it counts as clients than the businesses it services.
RIVALS
A spokesperson for the Australian Signals Directorate — the department of defense intelligence agency that bears the slogan “reveal their secrets, protect our own” — refused to confirm or deny use of Darktrace technology, saying it does not “provide commentary on capability or use of commercial products.”
There are certainly plenty of rivals to Darktrace technology also promoting their cybersecurity platform’s integration of the latest machine-learning capabilities, including CrowdStrike, Symantec and Cylance.
Then there are Darktrace’s true rivals — hackers themselves.
Thomas LaRock, technical evangelist at information technology company SolarWinds, said that machine learning is a tool that can be used to attack just as easily as it can be used to defend.
“If it is possible to use machine learning to build a model that helps them launch cyberattacks with greater efficiency, then that’s what you can expect to happen,” he said. “Think of this as a spy game, where you have agents that go from one side to another. There is bound to be a person somewhere right now working on machine-learning models to deter crime. One day they could be found to be working for the criminals, using machine learning models to help commit crime.”
Aurora defends the use of machine learning at Darktrace, saying this is one game companies cannot afford to opt out of.
“If you look at the way the threat landscape is moving, it is just simply humanly impossible using conventional methods — the only way to react to these threats is AI and machine learning,” he said. “We are proud to achieve on that front — pure, unsupervised machine learning, as employee behavior changes. That is the secret sauce — continuously evolving and learning.”

Because much of what former US president Donald Trump says is unhinged and histrionic, it is tempting to dismiss all of it as bunk. Yet the potential future president has a populist knack for sounding alarums that resonate with the zeitgeist — for example, with growing anxiety about World War III and nuclear Armageddon. “We’re a failing nation,” Trump ranted during his US presidential debate against US Vice President Kamala Harris in one particularly meandering answer (the one that also recycled urban myths about immigrants eating cats). “And what, what’s going on here, you’re going to end up in World War
Earlier this month in Newsweek, President William Lai (賴清德) challenged the People’s Republic of China (PRC) to retake the territories lost to Russia in the 19th century rather than invade Taiwan. He stated: “If it is for the sake of territorial integrity, why doesn’t [the PRC] take back the lands occupied by Russia that were signed over in the treaty of Aigun?” This was a brilliant political move to finally state openly what many Chinese in both China and Taiwan have long been thinking about the lost territories in the Russian far east: The Russian far east should be “theirs.” Granted, Lai issued
On Tuesday, President William Lai (賴清德) met with a delegation from the Hoover Institution, a think tank based at Stanford University in California, to discuss strengthening US-Taiwan relations and enhancing peace and stability in the region. The delegation was led by James Ellis Jr, co-chair of the institution’s Taiwan in the Indo-Pacific Region project and former commander of the US Strategic Command. It also included former Australian minister for foreign affairs Marise Payne, influential US academics and other former policymakers. Think tank diplomacy is an important component of Taiwan’s efforts to maintain high-level dialogue with other nations with which it does

On Sept. 2, Elbridge Colby, former deputy assistant secretary of defense for strategy and force development, wrote an article for the Wall Street Journal called “The US and Taiwan Must Change Course” that defends his position that the US and Taiwan are not doing enough to deter the People’s Republic of China (PRC) from taking Taiwan. Colby is correct, of course: the US and Taiwan need to do a lot more or the PRC will invade Taiwan like Russia did against Ukraine. The US and Taiwan have failed to prepare properly to deter war. The blame must fall on politicians and policymakers