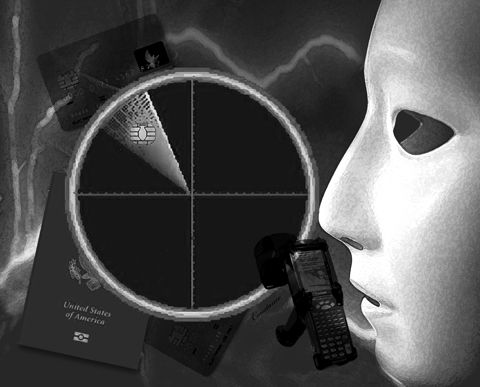
Climbing into his Volvo, outfitted with a Matrics antenna and a Motorola reader he had bought on eBay for US$190, Chris Paget cruised the streets of San Francisco with this objective: To read the identity cards of strangers, wirelessly, without ever leaving his car.
It took him 20 minutes to strike hacker’s gold.
Zipping past Fisherman’s Wharf, his scanner downloaded to his laptop the unique serial numbers of two pedestrians’ electronic US passport cards embedded with radio frequency identification (RFID) tags. Within an hour, he’d “skimmed” four more of the new PASS Cards from a distance of 6m.
Increasingly, government officials are promoting the chipping of identity documents as a 21st century application of technology to speed up border crossings, safeguard credentials against counterfeiters and keep terrorists from sneaking into the country.
However, Paget’s February experiment demonstrated something privacy advocates had feared for years — that RFID, coupled with other technologies, means people can be tracked without their knowledge.
He filmed his heist and soon his video went viral on the Web, intensifying a debate over a push by government — federal and state — to put tracking technologies in identity documents and over their potential to erode privacy.
Putting a traceable RFID in every pocket has the potential to make everybody a blip on someone’s radar screen, critics say, and to redefine Orwellian government snooping for the digital age.
“Little Brother,” some are already calling it — even though elements of the global surveillance web they warn against exist only on drawing boards, neither available nor approved for use.
With advances in tracking technologies coming at an ever-faster rate, critics say it won’t be long before governments could be able to identify and track anyone in real time, 24/7, from a cafe in Paris to the shores of California.
On June 1, it became mandatory for US citizens entering the country by land or sea from Canada, Mexico, Bermuda and the Caribbean to present identity documents embedded with RFID tags, though conventional passports remain valid until they expire.
Among new options are the chipped “e-passport,” and the new, electronic PASS Card — credit-card sized, with the bearer’s digital photograph and a chip that can be scanned through a pocket, backpack or purse from 9m.
Alternatively, travelers can use “enhanced” driver’s licenses embedded with RFID tags now being issued in some border states: Washington, Vermont, Michigan and New York.
Texas and Arizona have entered into agreements with the federal government to offer chipped licenses, and the US Department of Homeland Security (DHS) has recommended expansion to non-border states. Kansas and Florida officials have received DHS briefings on the licenses, agency records showed.
The purpose of using RFID is not to identify people, said Mary Ellen Callahan, the department’s chief privacy officer, but “to verify that the identification document holds valid information about you.”
An RFID document that doubles as a US travel credential “only makes it easier to pull the right record fast enough, to make sure that the border flows and is operational” — even though a 2005 Government Accountability Office report found that government RFID readers often failed to detect travelers’ tags.
Critics warn that RFID-tagged identities will enable identity thieves and other criminals to commit “contactless” crimes against victims who won’t immediately know they have been violated.
Neville Pattinson, vice president for government affairs at Gemalto Inc, a major supplier of the chipped cards, is no RFID basher. He’s a board member of the Smart Card Alliance, an RFID industry group, and is serving on the DHS’ data privacy and integrity advisory committee.
In a 2007 article published by a newsletter for privacy professionals, Pattinson called the chipped cards vulnerable “to attacks from hackers, identity thieves and possibly even terrorists.”
RFID, he wrote, has a fundamental flaw — each chip is built to faithfully transmit its unique identifier “in the clear, exposing the tag number to interception during the wireless communication.”
Once a tag number is intercepted, “it is relatively easy to directly associate it with an individual,” Pattinson said. “If this is done, then it is possible to make an entire set of movements posing as somebody else without that person’s knowledge.”
Echoing these concerns were the AeA — the lobbying association for technology firms — the Smart Card Alliance, the Institute of Electrical and Electronics Engineers, the Business Travel Coalition and the Association of Corporate Travel Executives.
Meanwhile, DHS has been promoting broad use of RFID even though its own advisory committee on data integrity and privacy issued caveats.
In its 2006 draft report, the committee concluded that RFID “increases risks to personal privacy and security, with no commensurate benefit for performance or national security,” and recommended that “RFID be disfavored for identifying and tracking human beings.”
For now, chipped PASS Cards and enhanced driver’s licenses are not yet widely deployed in the US. To date, roughly 192,000 enhanced driver’s licenses have been issued in Washington, Vermont, Michigan and New York.
However, as more Americans carry them “you can bet that long-range tracking of people on a large scale will rise exponentially,”said Paget, a self-described “ethical hacker” who works as an Internet security consultant.
Gigi Zenk, a spokeswoman for the Washington State Department of Licensing, said Americans “aren’t that concerned about RFID” in a time when “tracking an individual is much easier through a cellphone.”
In the wake of the Sept. 11, 2001, attacks — and the finding that some terrorists entered the US using phony passports — the State Department proposed mandating that Americans and foreign visitors carry “enhanced” passport booklets, with microchips embedded in the covers.
In February 2005, when the State Department asked for public comment, it got an outcry — of the 2,335 comments received, 98.5 percent were negative, with 86 percent expressing security or privacy concerns, the department reported in an October 2005 notice in the Federal Register.
Identity theft and “fears that the US Government or other governments would use the chip to track and censor, intimidate or otherwise control or harm them” were of “grave concern,” it noted. Many Americans worried “that the information could be read at distances in excess of 10 feet [3m].”
Those citizens, it turns out, had cause.
Department records obtained by researchers at the University of California at Berkeley, under a Freedom of Information Act request, show that discussion about security concerns with the e-passport occurred as early as January 2003, but tests were not ordered until the department began receiving public criticism two years later.
Asked when testing was initiated, the State Department said only that “a battery of durability and electromagnetic tests were performed” by the National Institute of Standards and Technology, along with tests “to measure the ability of data on electronic passports to be surreptitiously skimmed or for communications with the chip reader to be eavesdropped,” testing which “led to additional privacy controls being placed on US electronic passports.”
In 2005, the department incorporated metallic fibers into the e-passport’s front cover to reduce the read range and added encryptions and a feature that required inspectors to optically scan the e-passport first for the chip to communicate wirelessly.
What of public concerns about the e-passport’s read range?
In its October 2005 Federal Register notice, the State Department reassured Americans that the e-passport’s chip would emit radio waves only within a 10cm radius, making it tougher to hack.
However, in May 2006, at the University of Tel Aviv, researchers directly skimmed an encrypted tag from more than 1m away. At the University of Cambridge in Britain, a student intercepted a transmission between an e-passport and a legitimate reader from 49m.
The State Department, according to its own records, was aware of the problem months before its Federal Register notice and more than a year before the e-passport was rolled out in August 2006.
“Do not claim that these chips can only be read at a distance of 10cm,” Frank Moss, deputy assistant Secretary of State for passport services, wrote in an April 22, 2005, e-mail to Randy Vanderhoof, executive director of the Smart Card Alliance. “That really has been proven to be wrong.”
The chips could be skimmed from 1m away, he added — all a hacker would need to read e-passport numbers, say, in an elevator.
In February 2006, an encrypted Dutch e-passport was hacked on national television and later, British e-passports were hacked. The State Department countered that European e-passports weren’t as safe as their US counterparts because they lacked safety features, such as the anti-skimming cover. Recent studies have shown, however, that more powerful readers can penetrate that metal sheathing.
The RFIDs in enhanced driver’s licenses and PASS Cards contain a silicon computer chip attached to a wire antenna, which transmits a unique identifier via radio waves when “awakened” by an electromagnetic reader.
The technology they use is designed to track products through the supply chain. These chips, known as EPCglobal Gen 2, are intended to release their data to any inquiring Gen 2 reader within a 9m radius.
The government says remotely readable ID cards transmit only RFID numbers, which correspond to records stored in secure government databases. Even if a hacker were to copy an RFID number onto a blank tag and place it into a counterfeit ID, officials say, the forger’s face still wouldn’t match the true card holder’s photo in the database.
Still, computer experts say government databases can be hacked.
Others worry about a day when hackers might deploy readers at “chokepoints,” such as checkout lines, skim RFID numbers from people’s driver’s licenses, then pair those numbers to personal data skimmed from chipped credit cards (though credit cards are harder to skim). They imagine stalkers skimming RFID tags to track their targets and fear government agents compiling chip numbers at peace rallies, mosques or gun shows, simply by strolling through a crowd with a reader.
Others worry more about the linking of chips with other identification methods, including biometric technologies, such as facial recognition.
Should biometrics be coupled with RFID, “governments will have, for the first time in history, the means to identify, monitor and track citizens anywhere in the world in real time,” said Mark Lerner, spokesman for the Constitutional Alliance, a network of nonprofit groups, lawmakers and citizens opposed to remotely readable identity and travel documents.
The International Civil Aviation Organization, the UN agency that sets global standards for passports, has called for facial recognition in all e-passports.

Because much of what former US president Donald Trump says is unhinged and histrionic, it is tempting to dismiss all of it as bunk. Yet the potential future president has a populist knack for sounding alarums that resonate with the zeitgeist — for example, with growing anxiety about World War III and nuclear Armageddon. “We’re a failing nation,” Trump ranted during his US presidential debate against US Vice President Kamala Harris in one particularly meandering answer (the one that also recycled urban myths about immigrants eating cats). “And what, what’s going on here, you’re going to end up in World War
Earlier this month in Newsweek, President William Lai (賴清德) challenged the People’s Republic of China (PRC) to retake the territories lost to Russia in the 19th century rather than invade Taiwan. He stated: “If it is for the sake of territorial integrity, why doesn’t [the PRC] take back the lands occupied by Russia that were signed over in the treaty of Aigun?” This was a brilliant political move to finally state openly what many Chinese in both China and Taiwan have long been thinking about the lost territories in the Russian far east: The Russian far east should be “theirs.” Granted, Lai issued
On Tuesday, President William Lai (賴清德) met with a delegation from the Hoover Institution, a think tank based at Stanford University in California, to discuss strengthening US-Taiwan relations and enhancing peace and stability in the region. The delegation was led by James Ellis Jr, co-chair of the institution’s Taiwan in the Indo-Pacific Region project and former commander of the US Strategic Command. It also included former Australian minister for foreign affairs Marise Payne, influential US academics and other former policymakers. Think tank diplomacy is an important component of Taiwan’s efforts to maintain high-level dialogue with other nations with which it does

On Sept. 2, Elbridge Colby, former deputy assistant secretary of defense for strategy and force development, wrote an article for the Wall Street Journal called “The US and Taiwan Must Change Course” that defends his position that the US and Taiwan are not doing enough to deter the People’s Republic of China (PRC) from taking Taiwan. Colby is correct, of course: the US and Taiwan need to do a lot more or the PRC will invade Taiwan like Russia did against Ukraine. The US and Taiwan have failed to prepare properly to deter war. The blame must fall on politicians and policymakers