A specter is haunting the Internet but, outside of techie circles, nobody seems to be talking about it. The threat it represents to our security and wellbeing may be less dramatic than anything posed by global terrorism, but it has the potential to wreak much more havoc. And so far, nobody has come up with a good idea on how to counter it.
It's called the Storm Worm. It first appeared at the beginning of the year, hidden in e-mail attachments with the subject line: "230 dead as storm batters Europe." The PC of anyone who opened the attachment became infected and was secretly enrolled in an ever-growing network of compromised machines called a "botnet."
The term "bot" is a derivation of "software robot," which is another way of saying that an infected machine effectively becomes the obedient slave of its (illicit) owner.
If your PC is compromised in this way then, while you may own the machine, someone else controls it. And they can use it to send spam, to participate in distributed denial-of-service attacks on banks, e-commerce or government Web sites, or for other even more sinister purposes.
Storm has been spreading steadily since January, gradually constructing a huge botnet. It affects only computers running Microsoft Windows, but that means that more than 90 percent of the world's PCs are vulnerable. Nobody knows how big the Storm botnet has become, but reputable security professionals cite estimates of between 1 million and 50 million computers worldwide.
To date, the botnet has been used only intermittently, which is disquieting: What it means is that someone, somewhere, is quietly building a doomsday machine that can be rented out to the highest bidder, or used for purposes that we cannot yet predict.
Of course, computer worms are an old story, which may explain why the mainstream media has paid relatively little attention to what's been happening. Old-style worms -- the ones with names like Sasser and Slammer -- were written by vandals or hackers and designed to spread as quickly as possible. Slammer, for example, infected 75,000 computers in 10 minutes and therefore attracted a lot of attention. The vigor of the onslaught made it easier for anti-virus firms to detect the attack and come up with countermeasures. In that sense, old-style worms were like measles -- an infectious disease that shows immediate symptoms.
Storm is different. It spreads quietly, without drawing attention to itself. Symptoms don't appear immediately and an infected computer can lie dormant for a long time.
"If it were a disease, it would be more like syphilis, whose symptoms may be mild or disappear altogether, but which will come back years later and eat your brain," said one expert, Bruce Schneier.
Schneier said Storm represents "the future of malware" because of the technical virtuosity of its design. For example, it works rather like an ant colony, with separation of duties. Only a small fraction of infected hosts spread the worm. A much smaller fraction are command-and-control servers; the rest stand by to receive orders.
By only allowing a small number of hosts to propagate the virus and act as command-and-control servers, Storm is resilient against attack because even if those hosts shut down, the network remains largely intact.

KINGPIN: Marset allegedly laundered the proceeds of his drug enterprise by purchasing and sponsoring professional soccer teams and even put himself in the starting lineups Notorious Latin American narco trafficker Sebastian Marset, who eluded police for years, was handed over to US authorities after his arrest on Friday in Bolivia. Marset, a Uruguayan national who was on the US most-wanted list, was passed to agents of the US Drug Enforcement Administration at Santa Cruz airport in Bolivia, then put on a US airplane, Bolivian state television showed. “The arrest and deportation were carried out pursuant to a court order issued by the US justice system,” Bolivian Minister of Government Marco Antonio Oviedo told reporters. The alleged kingpin was arrested in an upscale neighborhood of Santa

ACTIONABLE ADVICE: The majority of chatbots tested provided guidance on weapons, tactics and target selections, with Perplexity and Meta AI deemed to be the least safe From school shootings to synagogue bombings, leading artificial intelligence (AI) chatbots helped researchers plot violent attacks, according to a study published on Wednesday that highlighted the technology’s potential for real-world harm. Researchers from the nonprofit watchdog Center for Countering Digital Hate and CNN posed as 13-year-old boys in the US and Ireland to test 10 chatbots, including ChatGPT, Google Gemini, Perplexity, Deepseek and Meta AI. Eight of the chatbots assisted the make-believe attackers in more than half the responses, providing advice on “locations to target” and “weapons to use” in an attack, the study said. The chatbots had become a “powerful accelerant for
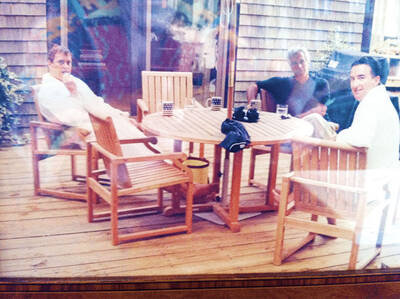
SCANDAL: Other images discovered earlier show Andrew bent over a female and lying across the laps of a number of women, while Mandelson is pictured in his underpants A photograph of former British prince Andrew and veteran politician Peter Mandelson sitting in bathrobes alongside late sex offender Jeffrey Epstein was unearthed on Friday in previously published documents. The image is believed to be the first known photograph of the two men with Epstein. They are currently engulfed in scandal in the UK over their ties to their mutual friend. The undated photograph, first reported by ITV News, shows King Charles III’s disgraced brother and former British ambassador to the US sitting barefoot outside on a wooden deck. They appear to have mugs with a US flag on them

Since the war in the Middle East began nearly two weeks ago, the telephone at Ron Hubbard’s bomb shelter company in Texas has not stopped ringing. Foreign and US clients are rushing to buy his bunkers, seeking refuge in case of air raids, nuclear fallout or apocalypse. With the US and Israel pounding Iran, and Tehran retaliating with strikes across the region, Hubbard has seen demand for his product soar, mostly from Gulf nation customers in Bahrain, Qatar, Kuwait and the United Arab Emirates. “You can imagine how many people are thinking: ‘I wish I had a bomb shelter,’” Hubbard, 63, said in