Last Wednesday, US Secretary of Defense Robert Gates announced the US was finally getting its act together on cyber-warfare. After a couple of false starts and a good deal of bureaucratic infighting, the Pentagon is setting up a unified US Cyber Command to oversee protection of military networks against cyber threats. It will be called USCybercom and will be led by the director of the National Security Agency, Lieutenant General Keith Alexander.
In a memo to the joint chiefs of staff, Gates said he had directed General Kevin Chilton, head of US Strategic Command, to develop implementation plans for the new command, which he wants on his desk by the beginning of September. Gates says that he expects USCybercom to be up and running by October and to have reached “full operating capability” within a year. That is light speed by federal government standards, so you can bet something’s up.
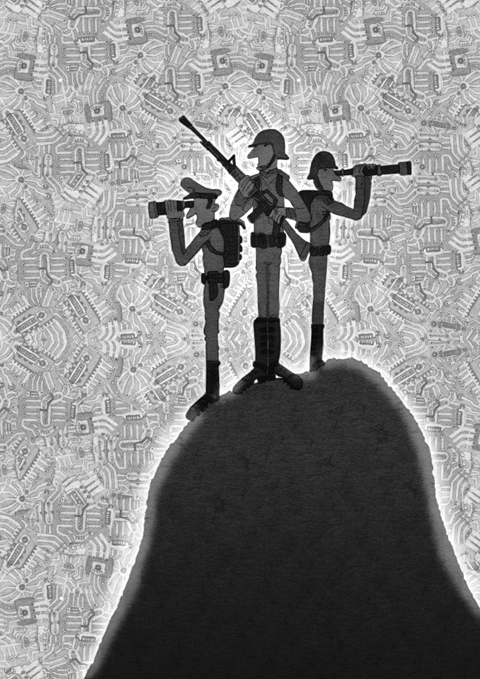
What it signifies is official recognition by the administration of President Barack Obama that the world has embarked on a new arms race. The weapons this time are malicious data-packets of the kind hitherto employed mainly by spammers, malware programmers, phishers, hackers and criminals. But whereas those operators are in business for mischief or private gain, nations will use their cyber-tools to wreak economic havoc and social disruption.
We’ve already had a case study of how it will work. Two years ago, Estonia experienced a sustained cyber-attack. It happened during a period of tension between Estonia and Russia.
“For the first time,” The Economist reported, “a state faced a frontal, anonymous attack that swamped the websites of banks, ministries, newspapers and broadcasters; that hobbled Estonia’s efforts to make its case abroad. Previous bouts of cyber-warfare have been far more limited by comparison: probing another country’s Internet defenses, rather as a reconnaissance plane tests air defenses.”
The onslaught was of a sophistication not seen before, with tactics shifting as weaknesses emerged. Individual “ports” (firewall gates) of mission-critical computers in, for example, Estonia’s telephone exchanges were targeted. The emergency number used to call ambulance and fire services was out of action for more than an hour. And so on.
It was a chilling demonstration of what is now possible, and it made governments sit up and take notice. Estonia is a member of NATO and the alliance responded by setting up a specialist cyber-warfare base in the country. Its code name is K5 and British reporter Bobbie Johnson visited it this year.
Johnson recounts what one of the staff told him about how NATO would react to another cyber-strike: “Overwhelming response: a single, gigantic counterstrike that cripples the target and warns anyone else off launching a future cyber-war. He isn’t sure what it would look like, but the show of force he envisages is so severe that the only thing he can compare it to is a nuclear attack.”
Hyperbole maybe, but all military establishments are tooling up. Last Thursday, British Prime Minister Gordon Brown revealed that his government had set up a “strategic” unit within the Government Communications Headquarters (GCHQ). Lord West, the retired admiral drafted in to the Home Office to look after security, told the BBC that “the government had developed the capability to strike back at cyber attacks,” though he declined to say if it had ever been used.
If Chinese, Russian, Israeli and Iranian ministers were free to speak on the subject, the message would be much the same.
If you’re not worried, you have not been paying attention. Almost without realizing it, our societies have become hugely dependent on a functioning, reliable Internet.
Life would go on without it, but most people would be shocked by how difficult much of the routine business of living would become. It would be like being teleported back to the 1970s. Even a minor conflict could slow the global Internet to a crawl. So cyber-war is a bit like nuclear war, in that even a minor outbreak threatens everyone’s life and welfare.
In those circumstances, isn’t it time we thought about devising treaties to regulate it? We need something analogous to the 1925 Geneva Protocol to the Hague Convention, which prohibited chemical and biological weapons. And we need to start now.

KMT Chairwoman Cheng Li-wun’s (鄭麗文) recent visit to Beijing and her upcoming visit to Washington will serve as a high-level test of her diplomatic mettle. In Beijing, Cheng was received with symbolic gestures, a warm reception, and high-level access. In Washington, she will receive far less pomp and far sharper questions about the KMT’s vision for the future of Taiwan. Her challenge will be to persuade Washington that the KMT’s engagement with China can coexist with strong deterrence. Cheng’s April 7-12 visit to mainland China coincided with an intense period of conflict in Iran. Despite the strategic significance of Cheng’s trip,

The closure of the Strait of Hormuz has sent the vast Asian chemicals industry into a tailspin. Deprived of the likes of Qatari natural gas and Saudi Arabian oil, the region’s fertilizer and plastics plants are slowing production or even shutting down. Everywhere except China, that is. In petrochemicals, China is unique. As well as a traditional industry that uses oil and gas as feedstock, it has parallel output that relies on its abundant domestic coal. Unsurprisingly, India and other regional powers want to copy and paste the Chinese method. This would not be easy — or climate friendly. The
History might remember 2026, not 2022, as the year artificial intelligence (AI) truly changed everything. ChatGPT’s launch was a product moment. What is happening now is an anthropological moment: AI is no longer merely answering questions. It is now taking initiative and learning from others to get things done, behaving less like software and more like a colleague. The economic consequence is the rise of the one-person company — a structure anticipated in the 2024 book The Choices Amid Great Changes, which I coauthored. The real target of AI is not labor. It is hierarchy. When AI sharply reduces the cost
US President Donald Trump recently repeated his claim that “Taiwan stole America’s chip industry,” reigniting public debate on the issue. As a former Taiwanese minister of economic affairs and an entrepreneur deeply involved in semiconductor supply chain development, I feel a responsibility to clarify this misunderstanding. From the perspective of global industrial evolution and the economic principle of comparative advantage, such a statement appears overly simplistic and risks obscuring the essence of the issue. The rise of Taiwan’s semiconductor industry was not built on “replacing America,” but rather emerged as a result of countries pursuing different development paths within the