Hackers are increasingly hiding viruses in bogus computer security software to trick people into installing treacherous programs on machines, Microsoft warned yesterday.
The software giant said in a security intelligence report that “rogue security software” is a growing threat as hackers take advantage of people’s fears of worms such as the notorious Conficker.
“Rogue security software is the number one threat worldwide,” said George Stathakopoulos, general manager of the Trustworthy Computing Group at Microsoft.
“If you think about the Conficker case, how many people went looking for a security solution and downloaded rogue malware?” he said.
Rogue security software referred to as “scareware” pretends to check computers for viruses and then claims to find dangerous infections that the program will fix for a fee.
“The rogue software lures them into paying for protection that, unknown to them, is actually malware offering little or no real protection, and is often designed to steal personal information,” Microsoft said.
Two “rogue families” of scareware were detected in 1.5 million computers, Microsoft said. Another form of scareware was found on 4.4 million computers, a rise of 66 percent from the previous six-month period.
“That means when users downloaded the software they probably gave away credit card numbers and got infected,” Stathakopoulos said. “That’s a double hit.”
Microsoft releases security reports twice annually. Stathakopoulos expects scareware infections to soar in the first six months of this year because of massive hype regarding Conficker.
The Conficker worm’s April 1st trigger date came and went without the bedeviling computer virus causing any mischief but security specialists warn that the threat is far from over.
The virus evolved on April Fools’ Day to better resist extermination and make its masters tougher to find.
A task force assembled by Microsoft has been working to stamp out Conficker, also referred to as DownAdUp, and the software colossus has placed a bounty of 250,000 dollars on the heads of those responsible for the threat.
The worm takes advantage of networks or computers that haven’t kept up to date with security patches for Windows.
It can infect machines from the Internet or by hiding on USB memory sticks carrying data from one computer to another.
Conficker could be triggered to steal data or turn control of infected computers over to hackers amassing “zombie” machines into “botnet” armies.
The report found that as operating system defenses improve, cybercriminals have shifted attacks to software applications people use in their online lives.
Ruses such as bogus software updates or security checks and booby-trapped Web pages or e-mails are among “social engineering” scams hackers use to dupe people into allowing malicious software past computer defenses.
“Cybercriminals [are] increasingly going after vulnerabilities in human nature,” said Vinny Gullotto, general manager of the Microsoft Malware Protection Center.

ROLLER-COASTER RIDE: More than five earthquakes ranging from magnitude 4.4 to 5.5 on the Richter scale shook eastern Taiwan in rapid succession yesterday afternoon Back-to-back weather fronts are forecast to hit Taiwan this week, resulting in rain across the nation in the coming days, the Central Weather Administration said yesterday, as it also warned residents in mountainous regions to be wary of landslides and rockfalls. As the first front approached, sporadic rainfall began in central and northern parts of Taiwan yesterday, the agency said, adding that rain is forecast to intensify in those regions today, while brief showers would also affect other parts of the nation. A second weather system is forecast to arrive on Thursday, bringing additional rain to the whole nation until Sunday, it

LANDSLIDES POSSIBLE: The agency advised the public to avoid visiting mountainous regions due to more expected aftershocks and rainfall from a series of weather fronts A series of earthquakes over the past few days were likely aftershocks of the April 3 earthquake in Hualien County, with further aftershocks to be expected for up to a year, the Central Weather Administration (CWA) said yesterday. Based on the nation’s experience after the quake on Sept. 21, 1999, more aftershocks are possible over the next six months to a year, the agency said. A total of 103 earthquakes of magnitude 4 on the local magnitude scale or higher hit Hualien County from 5:08pm on Monday to 10:27am yesterday, with 27 of them exceeding magnitude 5. They included two, of magnitude

CONDITIONAL: The PRC imposes secret requirements that the funding it provides cannot be spent in states with diplomatic relations with Taiwan, Emma Reilly said China has been bribing UN officials to obtain “special benefits” and to block funding from countries that have diplomatic ties with Taiwan, a former UN employee told the British House of Commons on Tuesday. At a House of Commons Foreign Affairs Committee hearing into “international relations within the multilateral system,” former Office of the UN High Commissioner for Human Rights (OHCHR) employee Emma Reilly said in a written statement that “Beijing paid bribes to the two successive Presidents of the [UN] General Assembly” during the two-year negotiation of the Sustainable Development Goals. Another way China exercises influence within the UN Secretariat is
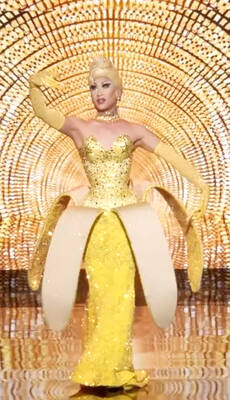
Taiwan’s first drag queen to compete on the internationally acclaimed RuPaul’s Drag Race, Nymphia Wind (妮妃雅), was on Friday crowned the “Next Drag Superstar.” Dressed in a sparkling banana dress, Nymphia Wind swept onto the stage for the final, and stole the show. “Taiwan this is for you,” she said right after show host RuPaul announced her as the winner. “To those who feel like they don’t belong, just remember to live fearlessly and to live their truth,” she said on stage. One of the frontrunners for the past 15 episodes, the 28-year-old breezed through to the final after weeks of showcasing her unique