The 13th Hacks In Taiwan Conference (HITCON), on Friday and Saturday last week at Academia Sinica, focused on malware Mirai and other potential loopholes in Internet security, such as trojaned subtitle files, while some attendees focused on larger issues, such as potential hacking of Internet of Things (IoT) applications and companies’ intranet servers.
Check Point Software Technologies vulnerability research team leader Omri Herscovici and Check Point security researcher Omer Gull gave a presentation on embedded coding in the subtitle file that enables hackers to spy on users or launch programs remotely.
Tan Kean Siong, an independent security researcher, honeypot hobbyist and member of the Honeynet Project — a “honeypot” refers to the digital baiting of enemy hackers — shared the results of an 18-month home-based Io Toney pot test he ran in 2015.
His team designed a fake device connected to the IoT for fun and deployed it as a single home-based honeypot sensor with Universal Plug and Play (UPnP) and Message Queue Telemetry Transport protocol emulation, Tan said.
After the Mirai botnet attacks this year, they found that their simulated IoT device received 6 million UPnP requests and was made to “assist” in denial of service attacks.
Most IoT applications lack firmware and software updates, which proves problematic in systems’ continued defense against virus and malware coding, Tan said, adding that he wished to draw attention to the importance of protecting information security on IoT devices.
The malware Mirae targets networked devices running Linux systems into remotely controlled “bots” that take part in large-scale network attacks.
It was first detected in August last year by MalwareMustDie, a whitehat malware research group.
Taiwanese white hat hacker Orange Tsai (蔡政達) gave a presentation on how hackers could still initiate server-side request forgery (SSRF) attacks on companies.
It might be a basic hack in the current age, but the more expansive a company’s intranet becomes, the more havoc such attacks could wreak, Tsai said, adding that as most service providers do not offer real-time updates, such basic attacks are still quite effective.
SSRF refers to an attack in which an attacker is able to send a crafted request from a vulnerable Web application, usually to target internal systems behind firewalls that are normally inaccessible to an attacker on an external network.
Meanwhile, HITCON announced the results of its ZeroDay platform program, which it hopes to become a trusted intermediary between white hat hackers and corporations.
“We hope to facilitate communication between the government, corporations and information security groups, as well as foster more individuals skilled in information security,” HITCON said in a statement.
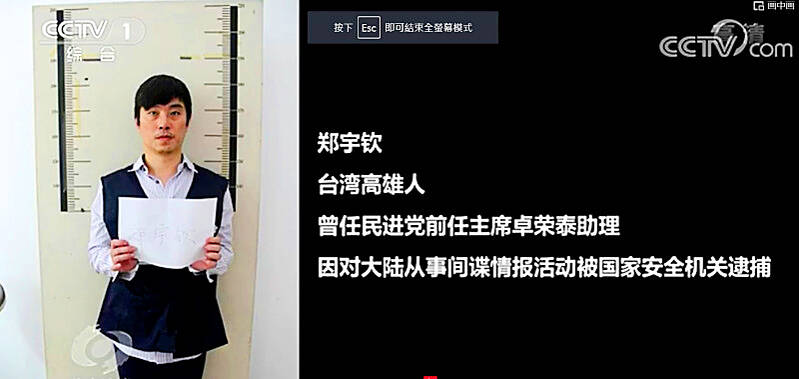
Former Czech Republic-based Taiwanese researcher Cheng Yu-chin (鄭宇欽) has been sentenced to seven years in prison on espionage-related charges, China’s Ministry of State Security announced yesterday. China said Cheng was a spy for Taiwan who “masqueraded as a professor” and that he was previously an assistant to former Cabinet secretary-general Cho Jung-tai (卓榮泰). President-elect William Lai (賴清德) on Wednesday last week announced Cho would be his premier when Lai is inaugurated next month. Today is China’s “National Security Education Day.” The Chinese ministry yesterday released a video online showing arrests over the past 10 years of people alleged to be

THE HAWAII FACTOR: While a 1965 opinion said an attack on Hawaii would not trigger Article 5, the text of the treaty suggests the state is covered, the report says NATO could be drawn into a conflict in the Taiwan Strait if Chinese forces attacked the US mainland or Hawaii, a NATO Defense College report published on Monday says. The report, written by James Lee, an assistant research fellow at Academia Sinica’s Institute of European and American Studies, states that under certain conditions a Taiwan contingency could trigger Article 5 of NATO, under which an attack against any member of the alliance is considered an attack against all members, necessitating a response. Article 6 of the North Atlantic Treaty specifies that an armed attack in the territory of any member in Europe,

LIKE FAMILY: People now treat dogs and cats as family members. They receive the same medical treatments and tests as humans do, a veterinary association official said The number of pet dogs and cats in Taiwan has officially outnumbered the number of human newborns last year, data from the Ministry of Agriculture’s pet registration information system showed. As of last year, Taiwan had 94,544 registered pet dogs and 137,652 pet cats, the data showed. By contrast, 135,571 babies were born last year. Demand for medical care for pet animals has also risen. As of Feb. 29, there were 5,773 veterinarians in Taiwan, 3,993 of whom were for pet animals, statistics from the Animal and Plant Health Inspection Agency showed. In 2022, the nation had 3,077 pediatricians. As of last

XINJIANG: Officials are conducting a report into amending an existing law or to enact a special law to prohibit goods using forced labor Taiwan is mulling an amendment prohibiting the importation of goods using forced labor, similar to the Uyghur Forced Labor Prevention Act (UFLPA) passed by the US Congress in 2021 that imposed limits on goods produced using forced labor in China’s Xinjiang region. A government official who wished to remain anonymous said yesterday that as the US customs law explicitly prohibits the importation of goods made using forced labor, in 2021 it passed the specialized UFLPA to limit the importation of cotton and other goods from China’s Xinjiang Uyghur region. Taiwan does not have the legal basis to prohibit the importation of goods