I had signed up to become a hacker for the day. I had no idea what to expect, or how difficult it might be. But it turned out that the hardest part about taking control of somebody else’s computer was just getting my own laptop connected to the internet — which indicates the scale of the security problem that we all face.
Our master class was trying to accurately simulate hacking into a decrepit Windows XP computer in the office of a multinational corporation, and Michael Belton, head of the penetration testing team at cybersecurity firm Rapid7, soon had me fully connected. And then the fun began.
‘’Penetration testing’’ is a euphemistic term for hacking. The crucial difference is that penetration testing is done with the permission of the network owner, so it is the digital equivalent of stores paying someone to shoplift from them to ensure their security staff are awake.

Photo: AFP
But if the motivations of the two are different, the methods — and end results — are the same. Which means that a penetration tester showing me the tools of his trade is a pretty good insight into how a script kiddie working with hacker collective like Anonymous goes about their business.
It also neatly answers the question of a Guardian editor who found out I was attending a ‘’hacking master class’’: Yes, it was legal, because we were only accessing systems with the permission of their owners. It’s when you start accessing everyone else’s that the problems begin.
1. We started with Linux
Once I arrived at our hacking venue, where Belton was going to demonstrate how to “own” a computer in just a couple of minutes, I was handed a USB stick with an installation of Kali Linux on it.
Linux is an open source operating system, a collectively-created free alternative to Mac OS or Windows, and Kali is a version of it designed specifically for penetration testers. It comes pre-installed with all the software necessary to take control of unsecured computers (and a good few secured ones as well), as well as all the standard productivity tools a team of testers would need to work together. Most importantly, it can be shrunk down small enough to fit on one thumbdrive — and can be booted straight from it.
That’s crucial for hackers, because although the temptation is to focus on their tools, the job is as much art as science. If you can get physical access to a network, there’s no need to bother trying to bypass firewalls from the outside.
Faking your way into a system
So penetration testers have been known to dress up as outside contractors, tail employees from smoking breaks, and even picking locks to get in the building. The Ethical Hackers Handbook, a guide for penetration testers, recommends practicing ahead of time the answers to common questions like ‘’I don’t think we’ve met; are you new?’’ and ‘’Who are you working for?’’
The same shortcuts apply elsewhere. If you’re trying to get hold of someone’s password, it’s far simpler to just get them to tell you than it is to crack their computer and read it from the memory.
These days, people tend to be more suspicious about unexpected phone calls asking for passwords. But there are other ways to achieve the same ends. Belton showed me software Rapid7 has produced which can easily fire off an email to every employee in a company, asking them to log in to a fake version of their own website. The program automatically strips all the assets from the real site, sets up a temporary server, and waits for people to input their passwords.
The whole thing is so convincing that when the company demonstrated it to a US senator who was visiting their offices, he immediately accused his head of press of being involved, despite having seen the entire process first hand.
2. Finding a way in, with Metasploit
But sometimes you just want to remotely take over a computer. What then?
The first thing to do is look for ways in. There are a number of such discovery tools, from SQLmap, which automatically looks for weaknesses in large databases, to Burpsuite, which is designed to take advantage of web application, but the one we were using was nMap, a type of program known as a port scanner.
Such applications are often likened to walking down the street, trying every door just to check if one is unlocked, but that slightly underestimates the scale of the thing. Services like nMap are more akin to walking through a city trying every door, window, and loose-looking brick while simultaneously making a note of how many locks they have, what type of key they take, and when it looks like they were built.
After just 45 seconds, the scan was done. It had identified our target: a computer running Windows XP Service Pack 2, released in 2004 and superseded by Service Pack 3 in 2008. (It was technically superseded by Windows Vista in 2007, but we don’t talk about Vista anymore.) Such a setup may seem like our poor sap — in reality a virtual machine running on Belton’s laptop — was being stitched up, but decade-old installations are depressingly common in the business world.
A few more keystrokes, and I launched the program which would get me inside: Metasploit.
The jewel in Rapid7’s arsenal, Metasploit is a one-stop-shop for cracking into computers. The program itself is over a decade old, but has been steadily updated with new vulnerabilities as time has gone on. It’s never at the cutting-edge, where security researchers are finding new holes, but what it lacks in currency it makes up for in ease-of-use.
Like all software for penetration testers, Metasploit has a strong contingent of users who are more interested in just seeing what they can break into. ‘’Let’s be honest, that’s what everyone uses it for,’’ says a Rapid7 PR sitting in on the master class.
With the help of Belton, I picked the particular faulty door which I would make my way through. According to nMap, our target was running a Microsoft program which comes installed on all XP computers and lets them share files back and forth. But version three of the software, which the target had, has a known vulnerability (‘’a parsing flaw in the path canonicalization code of NetAPI32.dll,’’ according to Rapid7). Using Metasploit, a single-line command exploits that flaw to load the third and final part of our assault, Meterpreter.
3. Taking control with Meterpreter
Running on the target computer, Meterpreter provides a backdoor through which I can take control of pretty much anything. The program never installs itself, running only in the memory, and only a particularly paranoid target will notice that their task monitor now shows a randomly named process. If even that’s too much risk, one further command can “inject’” Meterpreter inside another program so it stays invisible.
While I’m connected to Meterpreter, Metasploit presents me with a list of options. Some, like the ability to dump the contents of the memory or disable the mouse, are designed to let an attacker get further into the target network. The latter is a particularly cunning mix of electronic and human methods: disabling the mouse makes the user call IT support, who may then log in to the computer remotely or in person. Where you originally only had a user account, suddenly you have taken control of an administrator.
Others let you make the most of the access you already have. I can take a screenshot, record audio with a webcam, or livestream video. I can also set up a keylogger, and record everything the target types. If I want to, I don’t have to stop at Meterpreter; I can install further software, to sniff for credit card numbers, or permanently slave the computer to my own — perfect if I need to gather a few thousand together to bring down another site with a distributed denial of service attack, where a server is overwhelmed by the sheer weight of connections and breaks.
How to protect yourself
The scariest thing about it all isn’t what I can do. It’s that it’s me doing it. The software really is that simple. But a certain extent, that can be reassuring. The vast majority of the hackers we’re all so afraid of are actually doing little more than running a program which does the heavy lifting for them.
Protecting yourself against them is easy enough:
‧ Keep your computer up to date
‧ Try not to fall prey to phishing attempts
‧ And don’t run programs from untrusted sources
When it comes to drive-by hacks like the one I pulled off, you don’t have to be perfectly secure; just more secure than the poor sap who does fall prey. ‘’I don’t have to outrun the bear. I only have to outrun you.’’

In late October of 1873 the government of Japan decided against sending a military expedition to Korea to force that nation to open trade relations. Across the government supporters of the expedition resigned immediately. The spectacle of revolt by disaffected samurai began to loom over Japanese politics. In January of 1874 disaffected samurai attacked a senior minister in Tokyo. A month later, a group of pro-Korea expedition and anti-foreign elements from Saga prefecture in Kyushu revolted, driven in part by high food prices stemming from poor harvests. Their leader, according to Edward Drea’s classic Japan’s Imperial Army, was a samurai

The following three paragraphs are just some of what the local Chinese-language press is reporting on breathlessly and following every twist and turn with the eagerness of a soap opera fan. For many English-language readers, it probably comes across as incomprehensibly opaque, so bear with me briefly dear reader: To the surprise of many, former pop singer and Democratic Progressive Party (DPP) ex-lawmaker Yu Tien (余天) of the Taiwan Normal Country Promotion Association (TNCPA) at the last minute dropped out of the running for committee chair of the DPP’s New Taipei City chapter, paving the way for DPP legislator Su

Located down a sideroad in old Wanhua District (萬華區), Waley Art (水谷藝術) has an established reputation for curating some of the more provocative indie art exhibitions in Taipei. And this month is no exception. Beyond the innocuous facade of a shophouse, the full three stories of the gallery space (including the basement) have been taken over by photographs, installation videos and abstract images courtesy of two creatives who hail from the opposite ends of the earth, Taiwan’s Hsu Yi-ting (許懿婷) and Germany’s Benjamin Janzen. “In 2019, I had an art residency in Europe,” Hsu says. “I met Benjamin in the lobby
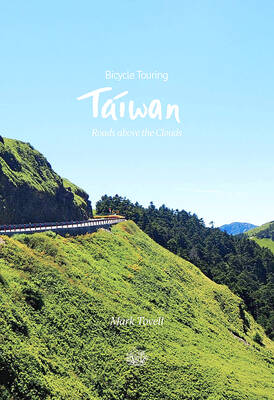
It’s hard to know where to begin with Mark Tovell’s Taiwan: Roads Above the Clouds. Having published a travelogue myself, as well as having contributed to several guidebooks, at first glance Tovell’s book appears to inhabit a middle ground — the kind of hard-to-sell nowheresville publishers detest. Leaf through the pages and you’ll find them suffuse with the purple prose best associated with travel literature: “When the sun is low on a warm, clear morning, and with the heat already rising, we stand at the riverside bike path leading south from Sanxia’s old cobble streets.” Hardly the stuff of your