They use screen aliases like IS Hunting Club, TouchMyTweets and The Doctor. They troll Twitter for suspected accounts of Islamic State fighters, recruiters and fundraisers.
Then they pounce.
In what has become a cyberanalogy to the battles in Syria, Iraq and elsewhere between governments and the Islamic State (IS), online vigilantes, some of them with diverse agendas, have united to subvert the militant group’s aggressive use of social media, particularly Twitter.
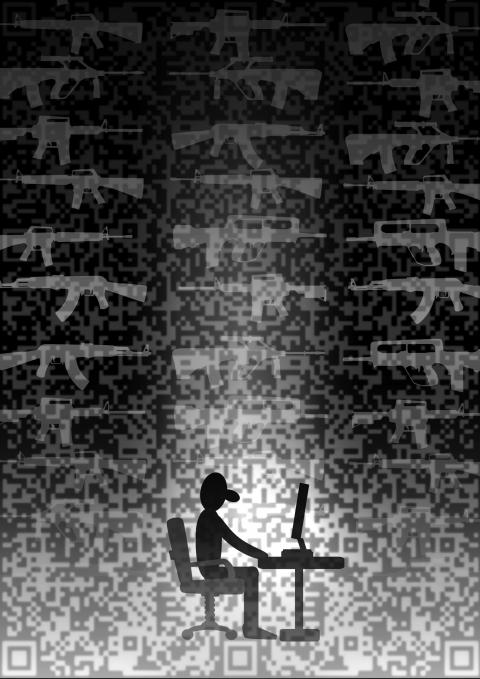
Illustration: Yusha
They expose suspect accounts that they post on blacklists via Twitter, and encourage other users to report the accounts to the social media network’s violations department, a prerequisite for suspension or deletion.
“Basically our work not only cripples their ability to spread propaganda, but also wastes their time,” a Twitter vigilante who goes by the screen name The Doctor said.
Like others, The Doctor communicated through private online chats. All asked that their real identities be withheld for their safety, as many have received death threats.
Some vigilantes are affiliated with loosely knit hacking organizations like Anonymous, known more for infiltrating computer networks of governments and corporations to make political statements or for the “lulz” — the hacker term for laughs. Others are lone operators.
However, all view groups like the Islamic State, previously known as the Islamic State of Iraq and the Levant, as an insidious threat. More than a few are women, some of whom call themselves “Anonymisses,” and some say they spend hours a day online hunting the Islamic State.
“I do this because the atrocities I see from these ISIS [Islamic State of Iraq and Syria] scum on a daily basis enrage me,” a user who identified herself as TouchMyTweets said, adding: “This is my airstrike.”
A loosely organized effort by computer hacking collectives aimed at disrupting the Islamic State and other violent militants causes began last year after extremists posted images of beheaded captives. It gained momentum after the Charlie Hebdo attack in Paris in January, according to experts who study online militants.
The effort is heavily focused on Twitter, which carries about 500 million messages a day, and has come under intense pressure because the Islamic State has shrewdly exploited it.
Critics, including cybersecurity experts and some members of the US Congress, contend Twitter has done little to stop the abuse. Twitter disputes that.
By some estimates, between 70,000 and 90,000 Twitter accounts are used by the Islamic State to spread images of beheadings and other brutalities, lure recruits and even relay battle positions — all with relative impunity because the system is free, enormous and, to a large extent, according to critics, unsupervised.
“There is a massive usage of Twitter underway by ISIS,” said Michael Smith, principal and chief operating officer of Kronos Advisory LLC, a security consulting company.
This month Anonymous and two related hacking groups, CntrlSec and GhostSec, have sought to take matters into their own hands, publicizing Twitter accounts that they say are operated by the Islamic State in violation of Twitter’s policies on unlawful use. In recent days they posted a list of 9,200 suspect accounts.
Some are calling it the battle between Anonymous and the Islamic State.
The hackers exhort other users to report the accounts to Twitter, and Twitter, which says it does not censor or proactively monitor message traffic, then decides whether to terminate the accounts.
When a suspect account is terminated, vigilantes celebrate by posting the account name and “#TangoDown” — the same language used by anti-terrorist commandos when they score a kill.
How many Twitter users are reporting suspect accounts because of this collaboration is unclear. Whether this vigilantism is significantly suppressing the use of Twitter by the Islamic State also has yet to be understood.
Asked for comment, Twitter said in an emailed statement: “We review all reported content against our rules, which prohibit unlawful use and direct, specific threats of violence against others.”
However, with the increased focus on use by the Islamic State, Twitter has suspended accounts at the rate of 2,000 per week recently, a company official said on condition of anonymity.
If the size of a Twitter account’s following is any indication, the hacking group GhostSec has a considerable force of activists behind it, with 6,274 as of Tuesday last week. CntrlSec had 2,039.
The Islamic State’s own cyberactivists have been anything but passive. They have threatened Twitter’s founder, Jack Dorsey, and his employees with death, posting ominous messages including a decapitated blue Twitter bird, the company’s icon.
People working on behalf of the Islamic State have taken countermeasures such as distributing lists of hackers to help avoid detection and urging followers to change account names if they suspect an impending complaint.
Late last month, militant accounts on Twitter began circulating a manual for bypassing Twitter requirements for the phone numbers and e-mail addresses of users, the SITE Intelligence Group, which monitors Islamic militancy online, reported a few weeks ago.
JM Berger, a nonresident fellow at the Brookings Institution who recently completed a study of Twitter use by Islamic State, said the campaign by vigilantes might be having some effect, although it was impossible to measure. The recently posted list of 9,200 Islamic State accounts, he said, is “the biggest catch they’ve put down.”
Smith expressed skepticism, asserting that the Twitter system still has thousands of Islamic State users.
A few weeks ago, senior members of the US House of Representatives Foreign Affairs Committee sent a bipartisan letter to Twitter chief executive Dick Costolo, urging him to increase efforts to combat groups like the Islamic State.
“Companies need to ensure that their social media services are not being hijacked for terrorist use,” the committee’s chairman, US Representative Ed Royce, wrote.
Twitter’s general counsel, Vijaya Gadde, responded in a letter, saying that the company had expanded its mechanisms for terminating accounts that violate its rules while preserving “the ability of users to share freely their views — including views that many people may disagree with or find abhorrent.”

Could Asia be on the verge of a new wave of nuclear proliferation? A look back at the early history of the North Atlantic Treaty Organization (NATO), which recently celebrated its 75th anniversary, illuminates some reasons for concern in the Indo-Pacific today. US Secretary of Defense Lloyd Austin recently described NATO as “the most powerful and successful alliance in history,” but the organization’s early years were not without challenges. At its inception, the signing of the North Atlantic Treaty marked a sea change in American strategic thinking. The United States had been intent on withdrawing from Europe in the years following
My wife and I spent the week in the interior of Taiwan where Shuyuan spent her childhood. In that town there is a street that functions as an open farmer’s market. Walk along that street, as Shuyuan did yesterday, and it is next to impossible to come home empty-handed. Some mangoes that looked vaguely like others we had seen around here ended up on our table. Shuyuan told how she had bought them from a little old farmer woman from the countryside who said the mangoes were from a very old tree she had on her property. The big surprise
The issue of China’s overcapacity has drawn greater global attention recently, with US Secretary of the Treasury Janet Yellen urging Beijing to address its excess production in key industries during her visit to China last week. Meanwhile in Brussels, European Commission President Ursula von der Leyen last week said that Europe must have a tough talk with China on its perceived overcapacity and unfair trade practices. The remarks by Yellen and Von der Leyen come as China’s economy is undergoing a painful transition. Beijing is trying to steer the world’s second-largest economy out of a COVID-19 slump, the property crisis and
As former president Ma Ying-jeou (馬英九) wrapped up his visit to the People’s Republic of China, he received his share of attention. Certainly, the trip must be seen within the full context of Ma’s life, that is, his eight-year presidency, the Sunflower movement and his failed Economic Cooperation Framework Agreement, as well as his eight years as Taipei mayor with its posturing, accusations of money laundering, and ups and downs. Through all that, basic questions stand out: “What drives Ma? What is his end game?” Having observed and commented on Ma for decades, it is all ironically reminiscent of former US president Harry