On the tiny Mediterranean island of Malta, two Italian hackers have been searching for bugs. Not the island’s many beetle varieties, but secret flaws in computer code that governments pay hundreds of thousands of dollars to learn about and exploit.
The hackers, Luigi Auriemma, 32, and Donato Ferrante, 28, sell technical details of such vulnerabilities to countries that want to break into the computer systems of foreign adversaries. The two will not reveal the clients of their company, ReVuln, but big buyers of services like theirs include the National Security Agency (NSA) — which seeks the flaws for the growing arsenal of US cyberweapons — and US adversaries like the Iranian Revolutionary Guard.
All over the world, from South Africa to South Korea, business is booming in what hackers call “zero days,” when the coding flaws in software like Microsoft’s Windows that can give a buyer unfettered access to a computer and any business, agency or individual dependent on one.
The flaws get their name from the fact that once discovered, “zero days” exist for the user of the computer system to fix them before hackers can take advantage of the vulnerability. A “zero-day exploit” occurs when hackers or governments strike by using the flaw before anyone else knows it exists, like a burglar who finds, after months of probing, that there is a previously undiscovered way to break into a house without sounding an alarm.
Just a few years ago, hackers like Auriemma and Ferrante would have sold the knowledge of coding flaws to companies like Microsoft and Apple, which would fix them. Last month, Microsoft sharply increased the amount it was willing to pay for such flaws, raising its top offer to US$150,000.
Increasingly, however, the businesses are being outbid by countries with the goal of exploiting the flaws in pursuit of the kind of success, albeit temporary, that the US and Israel achieved three summers ago when they attacked Iran’s nuclear enrichment program with a computer worm that became known as “Stuxnet.”
“Governments are starting to say, ‘In order to best protect my country, I need to find vulnerabilities in other countries,’” former White House cybersecurity coordinator Howard Schmidt said. “The problem is that we all fundamentally become less secure.”
A zero-day bug could be as simple as a hacker’s discovering an online account that asks for a password, but does not actually require typing one to get in. Bypassing the system by hitting the “Enter” key becomes a zero-day exploit. The average attack persists for almost a year — 312 days — before it is detected, according to Symantec, the maker of antivirus software. Until then it can be exploited or “weaponized” by both criminals and governments to spy on, steal from or attack their target.
Ten years ago, hackers would hand knowledge of such flaws to Microsoft and Google in exchange for a T-shirt or perhaps for an honorable mention on a company’s Web site. Even today, so-called patriotic hackers in China regularly hand over the information to the government.
Now, the market for information about computer vulnerabilities has turned into a gold rush. Disclosures by Edward Snowden, the former National NSA consultant who leaked classified documents, made it clear that the US is among the buyers of programming flaws. The US is hardly alone.
Israel, Britain, Russia, India and Brazil are some of the biggest spenders. North Korea is in the market, as are some Middle Eastern intelligence services. Countries in the Asian Pacific, including Malaysia and Singapore are buying too, according to the Center for Strategic and International Studies in Washington.
HACKER ECONOMICS
To connect sellers and buyers, dozens of well-connected brokers now market information on the flaws in exchange for a 15 percent cut. Some hackers get a deal collecting royalty fees for every month their flaw lies undiscovered, according to several people involved in the market. Some individual brokers, like one in Bangkok who goes by “the Grugq” on Twitter, are well known. After the Grugq spoke to Forbes last year his business took a hit from the publicity according to a person familiar with the impact, primarily because buyers demand confidentiality.
A broker’s approach need not be subtle. “Need code execution exploit urgent,” read the subject line of an e-mail sent from one contractor’s intermediary last year to Billy Rios, a former security engineer at Microsoft and Google who is now a director at Cylance, a security startup.
“Dear Friend,” the e-mail began. “Do you have any code execution exploit for Windows 7, Mac, for applications like Browser, Office, Adobe, SWF any.”
“If yes,” the e-mail continued, “payment is not an issue.”
For startups eager to displace more established military contractors, selling vulnerabilities — and expertise about how to use them — has become a lucrative opportunity. Firms like Vupen in Montpellier, France, Netragard in Acton, Massachusetts, Exodus Intelligence in Austin, Texas, and ReVuln, Auriemma and Ferrante’s Maltese firm, freely advertise that they sell knowledge of the flaws for cyberespionage and in some cases for cyberweapons.
Outside Washington, a Virginia startup named Endgame — in which a former director of the NSA is playing a major role — is more elusive about its abilities. It has developed a number of tools that it sells primarily to the US government to discover vulnerabilities, which can be used for fighting cyber-espionage and for offensive purposes.
Like ReVuln, none of the companies would disclose the names of customers. Adriel Desautels, the founder of Netragard, said that his clients were “strictly US-based” and that Netragard’s “exploit acquisition program” had doubled in size in the past three years. The average exploit now sells from around US$35,000 to US$160,000.
Chaouki Bekrar, the founder of Vupen, said his company did not sell to countries that are “subject to European Union, United States or United Nations restrictions or embargoes.” He also said revenue was doubling every year as demand surged for sophisticated exploits. Vupen charges customers an annual US$100,000 subscription fee to shop through its catalog of exploits, and then charges per exploit. Costs depend on the sophistication of the vulnerability and the pervasiveness of the operating system.
ReVuln specializes in finding remote vulnerabilities in industrial control systems that can be used to access — or disrupt — water treatment facilities, oil and gas pipelines and power plants.
“They are engaging in willful blindness,” said Christopher Soghoian, a senior policy analyst at the American Civil Liberties Union.
Many technology companies have started “bug bounty” programs in which they pay hackers to tell them about bugs in their systems rather than have the hackers keep the flaws to themselves — or worse, sell them on the black market. Nearly a decade ago the Mozilla Foundation started one of the first bounty programs to pay for bugs in its Firefox browser. Since then, Google, Facebook and PayPal have all followed suit. In recent months, bounties have soared.
In 2010, Google started paying hackers up to US$3,133.70 — the number is hacker code for “elite” — for bugs in its Web browser, Chrome. Last month, Google increased its cash prize to US$20,000 for exploits in some of its widely used products. Facebook began a similar program in 2011 and has since paid out US$1 million. One payout was US$2,500 to a 13-year-old. The most it has paid for a single bug is US$20,000.
“The program undermines the incentive to hold on to a bug that might be worth nothing in a day,” Facebook chief security officer Joe Sullivan said.
It also has the unintended effect of encouraging ethical hackers to turn in others who planned malicious use for bugs.
“We’ve seen people back-stab other hackers by ratting out a bug that another person planned to use maliciously,” he said.
Microsoft, which had long resisted such a program, did an about-face last month when it announced that it would pay hackers as much as US$150,000 for a single exploit, if they also provided a way to defend against it.
Apple still has no such program, but its vulnerabilities are some of the most coveted. In one case, a zero-day exploit in Apple’s iOS sold for US$500,000, according to two people briefed on the sale.
Still, Soghoian said, “The bounties pale in comparison to what the government pays.”
The military establishment, he said, “created Frankenstein by feeding the market.”
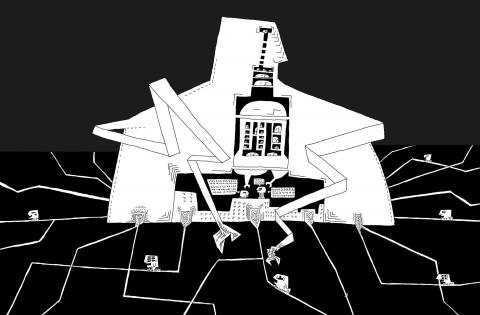
In many ways, the US government created the market. When the US and Israel used a series of flaws — including one in a Windows font program — to unleash the Stuxnet worm, a sophisticated cyberweapon used to temporarily cripple Iran’s ability to enrich uranium, it showed the world what was possible. It also became a catalyst for a cyberarms race.
IRANIAN TRIGGER
When the Stuxnet code leaked out of Iran’s Natanz nuclear enrichment plant in the summer of 2010, the flaws suddenly took on new value. Subsequent discoveries of sophisticated state-sponsored computer viruses named Flame and Duqu that used flaws to spy on computers in Iran have only fueled interest.
“I think it is fair to say that no one anticipated where this was going,” said one person who was involved in the early US and Israeli strategy. And today, no one is sure where it is going to end up.”
In a prescient paper in 2007, Charlie Miller, a former NSA employee, described the profitable alternatives for hackers who may have otherwise turned their information about flaws over to the vendor for free or sold it for a few thousand dollars to programs like Tipping Point’s Zero Day Initiative, now run by Hewlett-Packard, which used them to enhance their security research.
He described how one US government agency offered him US$10,000 for a Linux bug. He asked another for US$80,000, which agreed “too quickly,” Miller wrote. “I had probably not asked for enough.”
Because the bug did not work with a particular flavor of Linux, Miller eventually sold it for US$50,000. The take-away for him and his fellow hackers was clear: There was serious money to be made selling the flaws.
At their conventions, hackers started flashing signs that read, “No more free bugs.”
Hackers like Auriemma, who once gave away their bugs to software vendors and antivirus makers, now sound like union organizers declaring their rights.
“Providing professional work for free to a vendor is unethical,” Auriemma said. “Providing professional work almost for free to security companies that make their business with your research is even more unethical.”
Experts say there is limited incentive to regulate a market in which government agencies are some of the biggest participants.
“If you try to limit who you do business with, there’s the possibility you will get shut out,” Schmidt said. “If someone comes to you with a bug that could affect millions of devices and says, ‘You would be the only one to have this if you pay my fee,’ there will always be someone inclined to pay it.”
“Unfortunately,” he said, “dancing with the devil in cyberspace has been pretty common.”

Could Asia be on the verge of a new wave of nuclear proliferation? A look back at the early history of the North Atlantic Treaty Organization (NATO), which recently celebrated its 75th anniversary, illuminates some reasons for concern in the Indo-Pacific today. US Secretary of Defense Lloyd Austin recently described NATO as “the most powerful and successful alliance in history,” but the organization’s early years were not without challenges. At its inception, the signing of the North Atlantic Treaty marked a sea change in American strategic thinking. The United States had been intent on withdrawing from Europe in the years following
My wife and I spent the week in the interior of Taiwan where Shuyuan spent her childhood. In that town there is a street that functions as an open farmer’s market. Walk along that street, as Shuyuan did yesterday, and it is next to impossible to come home empty-handed. Some mangoes that looked vaguely like others we had seen around here ended up on our table. Shuyuan told how she had bought them from a little old farmer woman from the countryside who said the mangoes were from a very old tree she had on her property. The big surprise
The issue of China’s overcapacity has drawn greater global attention recently, with US Secretary of the Treasury Janet Yellen urging Beijing to address its excess production in key industries during her visit to China last week. Meanwhile in Brussels, European Commission President Ursula von der Leyen last week said that Europe must have a tough talk with China on its perceived overcapacity and unfair trade practices. The remarks by Yellen and Von der Leyen come as China’s economy is undergoing a painful transition. Beijing is trying to steer the world’s second-largest economy out of a COVID-19 slump, the property crisis and
Former president Ma Ying-jeou’s (馬英九) trip to China provides a pertinent reminder of why Taiwanese protested so vociferously against attempts to force through the cross-strait service trade agreement in 2014 and why, since Ma’s presidential election win in 2012, they have not voted in another Chinese Nationalist Party (KMT) candidate. While the nation narrowly avoided tragedy — the treaty would have put Taiwan on the path toward the demobilization of its democracy, which Courtney Donovan Smith wrote about in the Taipei Times in “With the Sunflower movement Taiwan dodged a bullet” — Ma’s political swansong in China, which included fawning dithyrambs