Wanted: experienced security professional. Must have plan to thwart Chinese counterfeiters, protect secret blueprints from spies and keep workers from leaving super-secret unreleased smartphones behind in bars.
A day after a recent report that an Apple employee had lost a prototype for a new, but unreleased, iPhone at a Northern California watering hole, two job listings appeared on Apple’s Web site for managers of “new product security.”
Such workers would join a team at the US$350 billion company that has included former FBI agents and other highly trained pros with backgrounds in intelligence and law enforcement.
While a private security force might not seem in keeping with its user-friendly image, Apple and other companies in its league need the best protection they can buy, corporate security experts say. Lost iPhones likely don’t come near the top of the list of anxieties.
“Corporate espionage, that’s big money, billion-dollar money. The paranoia is justified,” said Jim -Stickley, co-founder of corporate security consulting firm -TraceSecurity “Whatever they’re trying to do, their competitors want to know. Everybody wants to know.”
Apple watchers say the company is known for creating many test versions of its new devices before they’re released to see how they work in the real world.
Losing just one such device is perhaps more of a marketing headache than a serious security breach, as was the case for Apple last year when the tech blog Gizmodo posted photos of what turned out to be a then-unreleased iPhone 4 lost by an employee at a San Francisco Bay Area beer garden.
Once a new device has reached the point where employees are field-testing it, a competitor who obtained one wouldn’t have enough time to analyze it and do anything to take advantage of that insider knowledge, Stickley said.
However, for Apple and other tech companies the issue amounts not just to a publicity problem, but a fiduciary obligation to shareholders to secure the company’s valuable assets, Apple analyst Tim Bajarin said. Companies also have an obligation to try to prevent such a loss from happening again, he added.
“If they fail, it’s the system that failed as much as the individual,” he said.
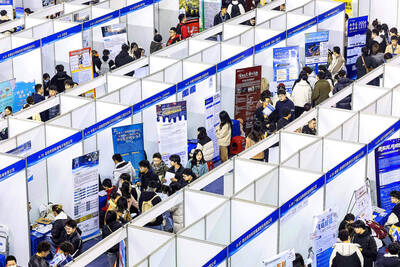
Despite the blogosphere frenzy surrounding the lost iPhone prototypes, experts say the security threats to tech companies are far more serious in China, where thousands of workers labor to manufacture Apple’s products.
According to a 2008 diplomatic cable released by WikiLeaks, Apple had only a modest security presence in China until March of that year, when the company hired a team from Pfizer that led a crusade against fake Viagra.
Under the leadership of Donald Shruhan, whose LinkedIn profile lists him as a Hong Kong-based senior regional director for Apple in security and investigations, the company began taking steps to rein in the country’s trade in counterfeit iPhones, iPods and MacBooks.
“Early evidence suggests nearly 100 percent of Apple products in unauthorized mainland markets are knockoffs,” according to the unclassified cable from the US embassy in Beijing.
The job of keeping such counterfeits off the shelves, to keep blueprints for new products from leaking and to otherwise secure vital trade secrets falls under the field of information assurance.
For information assurance professionals, securing computer networks is only part of the job. They also make sure companies remember to lock their actual doors.
“Social engineering” also remains a constant threat in the tech industry, said Gary Kessler, director of the information assurance program at Norwich University, a private military college in Vermont that has trained security personnel at Apple and other high-profile companies.
From e-mail scams seeking sensitive personal information to Cold War-style cloak-and-dagger subterfuge, human weakness can be easier to exploit and harder to protect against than digital vulnerabilities.
“This stuff has been going on for decades, just in a different guise,” Kessler said. “The Internet has just given us a new vector for attack.”
In the end, he said, even the best-trained security team in the world can only do so much to protect against someone in a bar who may have been drinking and may have been showing off the most sought-after secret product in the world.
“I’m guessing that Apple probably did everything that anybody could do, and they probably did it right,” Kessler said.
Stephen Garrett, a 27-year-old graduate student, always thought he would study in China, but first the country’s restrictive COVID-19 policies made it nearly impossible and now he has other concerns. The cost is one deterrent, but Garrett is more worried about restrictions on academic freedom and the personal risk of being stranded in China. He is not alone. Only about 700 American students are studying at Chinese universities, down from a peak of nearly 25,000 a decade ago, while there are nearly 300,000 Chinese students at US schools. Some young Americans are discouraged from investing their time in China by what they see

MAJOR DROP: CEO Tim Cook, who is visiting Hanoi, pledged the firm was committed to Vietnam after its smartphone shipments declined 9.6% annually in the first quarter Apple Inc yesterday said it would increase spending on suppliers in Vietnam, a key production hub, as CEO Tim Cook arrived in the country for a two-day visit. The iPhone maker announced the news in a statement on its Web site, but gave no details of how much it would spend or where the money would go. Cook is expected to meet programmers, content creators and students during his visit, online newspaper VnExpress reported. The visit comes as US President Joe Biden’s administration seeks to ramp up Vietnam’s role in the global tech supply chain to reduce the US’ dependence on China. Images on

New apartments in Taiwan’s major cities are getting smaller, while old apartments are increasingly occupied by older people, many of whom live alone, government data showed. The phenomenon has to do with sharpening unaffordable property prices and an aging population, property brokers said. Apartments with one bedroom that are two years old or older have gained a noticeable presence in the nation’s six special municipalities as well as Hsinchu county and city in the past five years, Evertrust Rehouse Co (永慶房產集團) found, citing data from the government’s real-price transaction platform. In Taipei, apartments with one bedroom accounted for 19 percent of deals last

US CONSCULTANT: The US Department of Commerce’s Ursula Burns is a rarely seen US government consultant to be put forward to sit on the board, nominated as an independent director Taiwan Semiconductor Manufacturing Co (TSMC, 台積電), the world’s largest contract chipmaker, yesterday nominated 10 candidates for its new board of directors, including Ursula Burns from the US Department of Commerce. It is rare that TSMC has nominated a US government consultant to sit on its board. Burns was nominated as one of seven independent directors. She is vice chair of the department’s Advisory Council on Supply Chain Competitiveness. Burns is to stand for election at TSMC’s annual shareholders’ meeting on June 4 along with the rest of the candidates. TSMC chairman Mark Liu (劉德音) was not on the list after in December last